A CHERI on Top: A Better Way to Build Embedded Secure SoCs
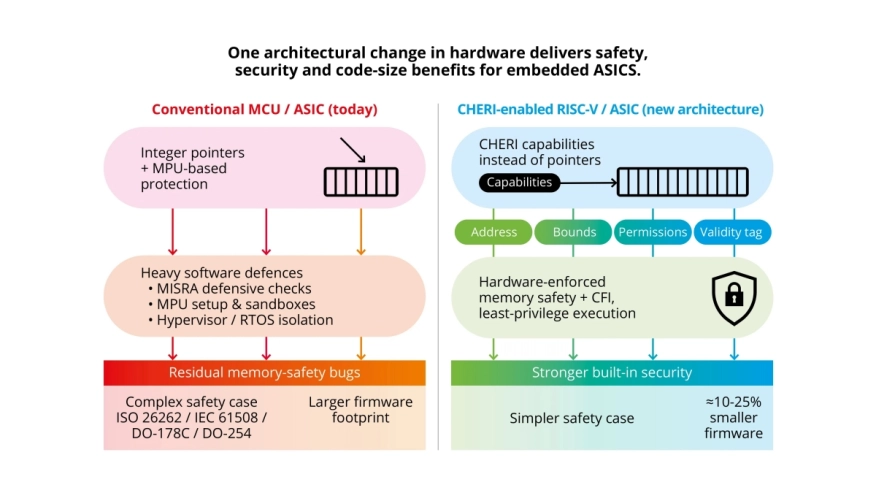
Hardware-enforced memory safety strengthens security, simplifies functional safety and even reduces firmware size.
Building safe and secure embedded systems is getting harder as firmware grows in scale, complexity, and connectivity. Even with sophisticated safeguards, such as microprocessor (MPU) regioning, real-time operating system (RTOS) isolation, static analysis tools, and strict coding standards (including MISRA C), application-specific IC (ASIC) and system-on-chip (SoC) developers still encounter the same architectural weakness: memory-safety violations. Buffer overruns, out-of-bounds accesses, and pointer corruption are consistently the leading sources of unpredictable system behavior and real-world security exploits.
CHERI began as a joint research effort between the University of Cambridge and SRI International, funded by DARPA, to prevent memory-safety vulnerabilities at the architectural level. Early MIPS prototypes proved that capabilities, pointers with hardware-enforced bounds and permissions, could be added without breaking C/C++ compatibility. The work later moved to RISC-V, demonstrating portability and modest hardware cost.
 Arm’s 2021 Morello program brought CHERI into a commercial-grade central processing unit (CPU) and SoC, enabling wider scale industry evaluation. Today, CHERI is regarded as a major advance in secure architecture, and CHERI extensions are now progressing through the RISC-V International standardization process, with multiple working groups defining how capabilities become an optional but interoperable part of future RISC-V profiles.
Arm’s 2021 Morello program brought CHERI into a commercial-grade central processing unit (CPU) and SoC, enabling wider scale industry evaluation. Today, CHERI is regarded as a major advance in secure architecture, and CHERI extensions are now progressing through the RISC-V International standardization process, with multiple working groups defining how capabilities become an optional but interoperable part of future RISC-V profiles.
To read the full article, click here
Related Semiconductor IP
- SHA-256 Secure Hash Algorithm IP Core
- EdDSA Curve25519 signature generation engine
- DeWarp IP
- 6-bit, 12 GSPS Flash ADC - GlobalFoundries 22nm
- LunaNet AFS LDPC Encoder and Decoder IP Core
Related Blogs
- Why Embedded MRAMs Are the Future for Advanced-Node SoCs
- ML-KEM explained: Quantum-safe Key Exchange for secure embedded Hardware
- ML-DSA explained: Quantum-Safe digital Signatures for secure embedded Systems
- Intel’s Atom-based Tunnel Creek SOC with integrated PCIe interface opens new era for embedded developers
Latest Blogs
- Area, Pipelining, Integration: A Comparison of SHA-2 and SHA-3 for embedded Systems.
- Why Your Next Smartphone Needs Micro-Cooling
- Teaching AI Agents to Speak Hardware
- SOCAMM: Modernizing Data Center Memory with LPDDR6/5X
- Bridging the Gap: Why eFPGA Integration is a Managed Reality, Not a Schedule Risk
