ECC IP
Filter
Compare
483
IP
from
71
vendors
(1
-
10)
-
ECC Secure Accelerator - High-performance ECC IP with advanced physical security
High-performance ECC IP with advanced physical security
-
ECC Secure Accelerator - Compact and Secure ECC IP Core for Resource-Constrained Devices
- Compact and Secure ECC IP Core for Resource-Constrained Devices
-
BCH ECC Core IP
- The patent-pending Dynamically Configurable BCH technology is the base for the BCH ECC engine incorporating BCH coders and decoders configurable for a wide range of code-length for high performance and high data rate error corrections.
- The BCH ECC engine with configurable code-length BCH coders and decoders performs the Inversion-less Berlekamp-Massey Algorithm (IBMA) to generate or decode the ECC code on each clock.
-
Elliptic Curve Cryptography IP
- Supported algorithms:
- Point multiplication
- ECDSA signature generation
- ECDSA signature verification
-
-
high-performance solution for elliptic curve cryptography
- Supported algorithms:
- Supported Elliptic Curves
- Optional Side Channel Attacks countermeasures
- Input/Output EC point verification
-
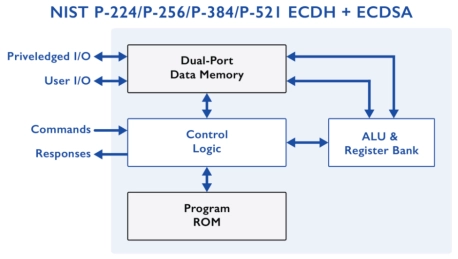
NIST P-256/P-384 ECDH+ECDSA - Compact ECC IP Cores supporting ECDH and ECDSA on NIST P-256/P-384
- Minimal Resource Requirements
- Secure Architecture
- FIPS 186-4 and SP 800-56A compliant
-
ECC with BCH Algorithm
- High bandwidth, low latency parallel encode and decode paths
- Configurable number of encode blocks
- Configurable number of decode blocks
- Configurable code word length (K), up to 1024 bytes
-
100% Secure Cryptographic System for RSA, Diffie-Hellman and ECC with AMBA AHB, AXI4 and APB
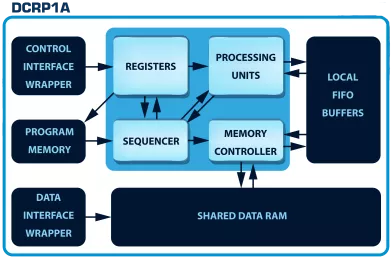
- The DCRP1A - CryptOne IP is a 100% secure cryptographic system
- CryptOne is a fully scalable, hardware-accelerated cryptographic system
- Designed for next-generation SoCs, FPGAs, and secure embedded systems, it delivers 100% secure asymmetric cryptography acceleration for demanding applications.
-
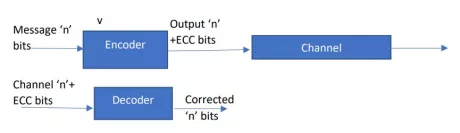
Error Correction Checking (ECC) Core
- Supports Single Bit Error correction and double bit error detection functions
- Supports hamming algorithm for 4 to 64 data widths
- Supports Hsiao algorithm for 4 to 128 data widths
- Supports encode only, decode only and encode/decode modes