100% Secure Cryptographic System for RSA, Diffie-Hellman and ECC with AMBA AHB, AXI4 and APB
CryptOne is a fully scalable, hardware-accelerated cryptographic system built on 20+ years of DCD-SEMI’s engineering experience.
Overview
CryptOne is a fully scalable, hardware-accelerated cryptographic system built on 20+ years of DCD-SEMI’s engineering experience. Designed for next-generation SoCs, FPGAs, and secure embedded systems, it delivers 100% secure asymmetric cryptography acceleration for demanding applications.
Supported algorithms include:
- Digital Signature algorithms
- RSA (up to 4096-bit keys) with optional CRT optimization
- Modular exponentiation
- Diffie–Hellman
- Elliptic Curve Cryptography (ECC) over GF(p)
- Miller–Rabin primality test
Performance That Outruns Competitive Designs
In benchmark tests, DCD’s architecture proved significantly more efficient than competing IP cores:
- Up to 25% fewer logic cells with equal performance
- Up to 50% higher performance when optimized for speed
This means engineers can achieve top-class cryptographic throughput while maintaining a smaller silicon footprint — crucial for cost-sensitive or power-constrained designs.
Ultimate ECC Performance (NIST P-256 @ 200 MHz)
- EC point multiplication: 2.5 ms
- ECDSA sign: 2.6 ms
- ECDSA verify: 3.2 ms
This level of acceleration makes CryptOne an ideal choice for secure boot, key exchange, firmware validation, IoT security modules, automotive ECUs, industrial controllers, and defense-grade electronics.
Energy-Efficient, Secure, and Easy to Integrate
CryptOne’s architecture is engineered for both high speed and ultra-low power, enabling advanced public-key operations on minimal silicon area.
Key advantages:
- Interfaces: AMBA AHB, AXI4, APB
- Fast, intuitive integration thanks to a clean, well-documented API
- Resistance to timing attacks
- Optional DPA countermeasures for high-security designs
- Full support for big number arithmetic (up to 4096 bits): modular multiplication, addition, subtraction, and shifts
With native acceleration for RSA, Diffie-Hellman, and ECC, CryptOne gives designers a unified, future-proof cryptographic engine ready for secure hardware architectures across consumer, industrial, and mission-critical applications.
Key features
- CryptOne constant time algorithms:
- Modular exponentiation,
- Parallel modular exponentiation CRT
- ECDSA sign/verify
- ECDH
- Elliptic curve point multiplication
- Modular multiplicative inverse
- GCD
- Modular reduction
- Multiplication
- Division
- Cryptographic algorithm applications:
- ECDSA, ECDH
- RSA key generation
- RSA Sign/Verify/Encrypt/Decrypt
- Diffie-Hellman schemes
- Miller-Rabin Primality check
- System applications:
- Client-server communication
- Sensor networks
- SSL/TLS stacks
- IoT devices
- Embedded security/ID devices
- AMBA AHB, AXI4, APB interface ready
- Rapid & easy development with delivered API
- Patent pending architecture
- Algorithms resistant against SPA and timing attacks
- CryptOne elliptic curves with native support:
- NIST P-192
- NIST P-224
- NIST P-256
- NIST P-384
- Koblitz P-192
- Koblitz P-256
- Koblitz P-384
- Brainpool P-256
- Brainpool P-384
- Brainpool P-512
- Other/custom curves optional support
- Software support:
- OpenSSL engine
- MbedTLS port
- OS independent crypto library
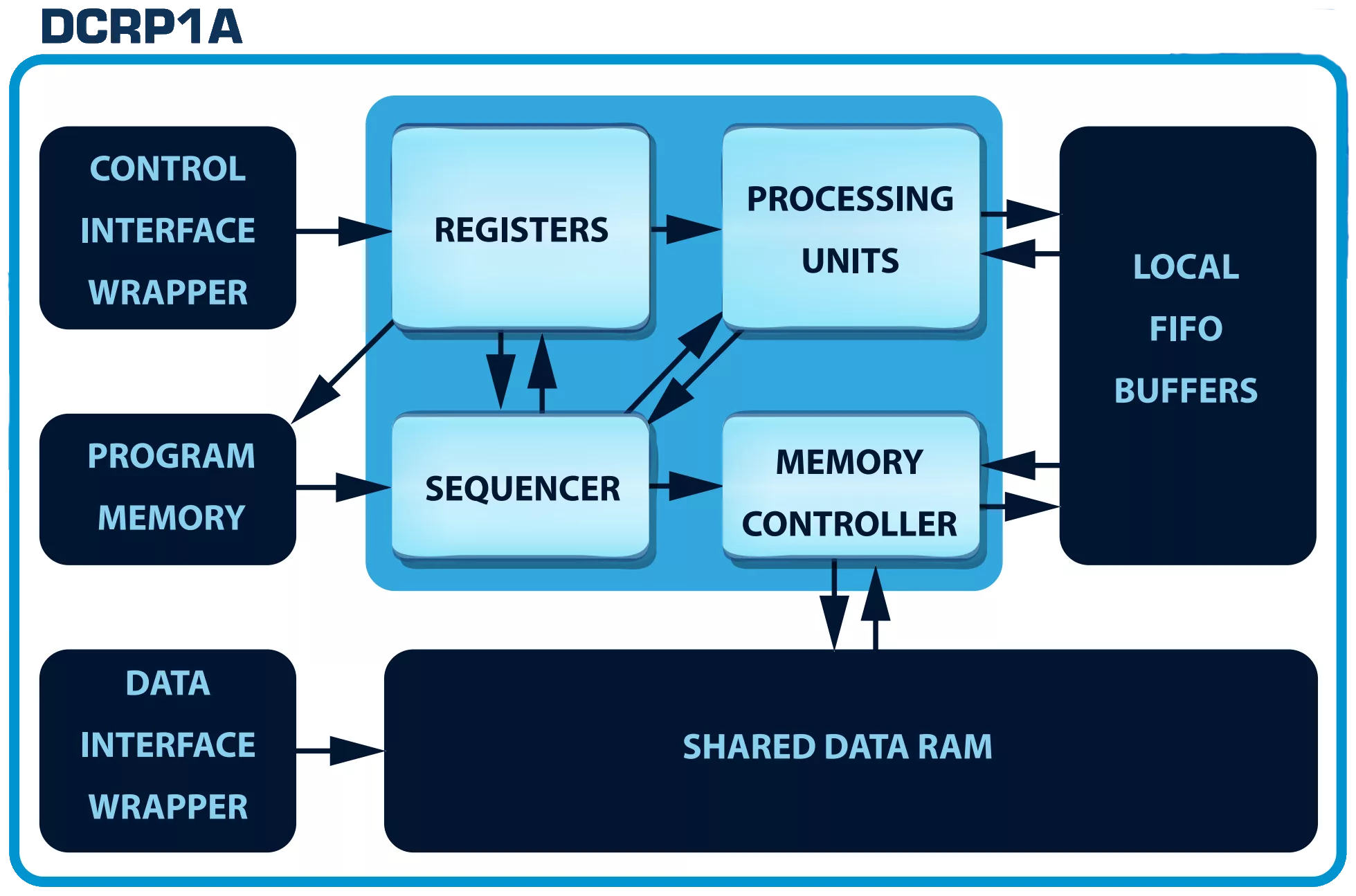
Block Diagram
Benefits
- Rapid prototyping and time-to-market reduction
- Design risk elimination
- Development costs reduction
- Full customization
- Global sales network
- Technology independence
- Professional service
- Getting a sillicon proven IP
Applications
- Client-server communication
- Sensor networks
- SSL/TLS stacks
- IoT devices
- Embedded security/ID devices
What’s Included?
- C software drivers with API
- Silicon proven architecture
- Hardware code:
- VERILOG Source Code
- VERILOG test bench environment
- Technical documentation
- Synthesis scripts
- 12 months of free technical support included
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Security
Provider

Learn more about Public Key IP core
Securing the IoT: Part 1 - Public key cryptography
Smart Engine for Public Key cryptography
Public key cryptography and security certificates
Securing your apps with Public Key Cryptography & Digital Signature
Formally verifying AVX2 rejection sampling for ML-KEM
Frequently asked questions about Public-Key Cryptography IP cores
What is 100% Secure Cryptographic System for RSA, Diffie-Hellman and ECC with AMBA AHB, AXI4 and APB?
100% Secure Cryptographic System for RSA, Diffie-Hellman and ECC with AMBA AHB, AXI4 and APB is a Public Key IP core from Digital Core Design listed on Semi IP Hub.
How should engineers evaluate this Public Key?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Public Key IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.