SM4 IP
Filter
Compare
30
IP
from
10
vendors
(1
-
10)
-
Security Protocol Accelerator for SM3 and SM4 Ciphers
- Highly customer configurable, silicon-proven security accelerator
- Support for Chinese security SM3 and SM4 (modes: ECB, CTR, CBC, CCM, GCM, XTS) algorithms
- Option: Differential Power Analysis (DPA) countermeasures for SM4
- Built-in scatter/gather DMA capability offloads the host processor
-
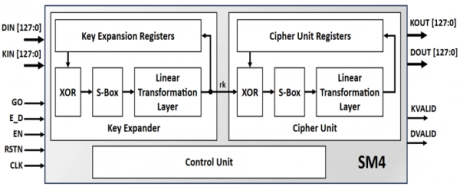
SM4 Encoder and Decoder
- Compliant with GBT.32907-2016
- Support both encryption and decryption
- Support ECB, CBC and multiple ciphering modes
-
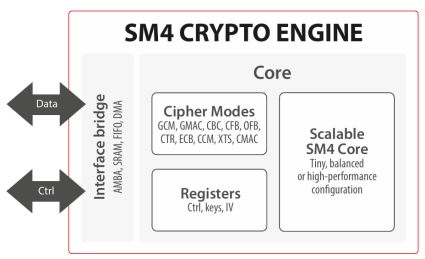
SM4 Crypto Engine
- The SM4 crypto engine includes a generic & scalable implementation of the SM4 algorithm which is the block cipher standard of China.
- It is compliant with the GBT.32907-2016 specification and can support several cipher modes including authenticated encryption.
-
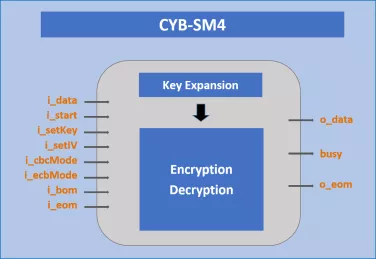
SM4 Cipher Engine
- The SM4 IP core implements a custom hardware accelerator for the SM4 symmetric block cipher, specified in Chinese national standard GB/T 32907-2016, and ISO/IEC 18033-3:2010/Amd 1:2021.
- Designed for easy integration, the core, internally expanding the 128-bit key, is capable of both encryption and decryption and features a simple handshake input and output data interface.
-
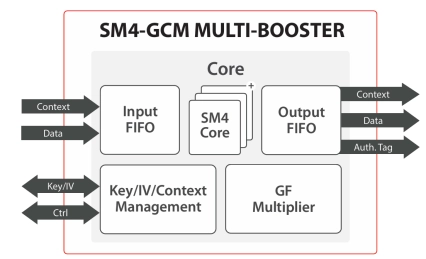
SM4-GCM Multi-Booster crypto engine
- ASIC & FPGA
- High throughput
- Guaranteed performance with small packets
-
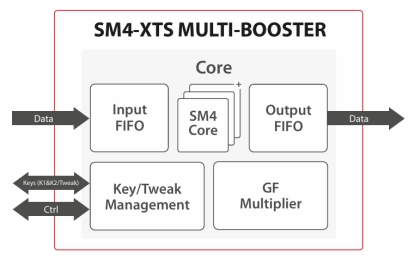
SM4-XTS Multi-Booster
- The SM4-XTS Multi-Booster crypto engine includes a generic & scalable implementation of the SM4 algorithm (a block cipher specified by the OSCCA) making the solution ideal for high-end applications (including key, tweak, input and output registers and Galois field multiplier).
-
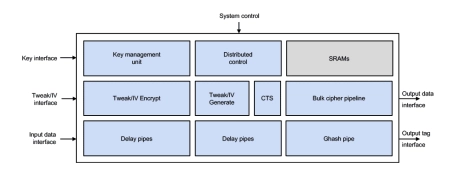
Fast Inline Cipher Engine, AES-XTS/GCM, SM4-XTS/GCM, DPA
- One input word per clock without any backpressure
- Design can switch stream, algorithm, mode, key and/or direction every clock cycle
- GCM: throughput is solely determined by the data width, data alignment and clock frequency
- XTS: block processing rate may be limited by the number of configured tweak encryption & CTS cores; a configuration allowing 1 block/clock is available
-
Cryptographic engine using the DES, Triple-DES or AES
- The cryptographic processor (CRYP) can be used both to encrypt and decrypt data using the DES, Triple-DES, AES or SM4 algorithms.
-
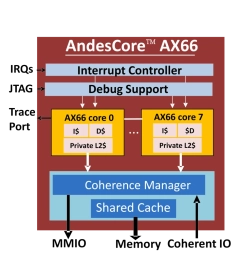
RVA23, Multi-cluster, Hypervisor and Android
- 64-bit out-of-order 4 wide decode 13-stage CPU core with 128 reordering buffers and 8 functional pipelines
- Symmetric multiprocessing up to 8 cores
- Private L2 cache support
- Level-3 shared cache and coherence support