xQlave® ML-KEM (Kyber) Key Encapsulation Mechanism IP core
xQlave® ML-KEM (Kyber) Key Encapsulation Mechanism IP core provides quantum-resistant key exchange, offering a secure solution ag…
Overview
xQlave® ML-KEM (Kyber) Key Encapsulation Mechanism IP core provides quantum-resistant key exchange, offering a secure solution against the growing threat posed by quantum computing. As a member of xQlave® Post-Quantum Cryptography (PQC) product family, this IP core is designed to meet the security standards set by the U.S. National Institute of Standards and Technology (NIST), ensuring that your systems are equipped to handle the cryptographic challenges of the future. The xQlave® ML-KEM PQC solution combines high performance with minimal resource usage, making it an ideal choice for secure, scalable, and efficient key exchange.
Key features
- Quantum-resistant key exchange for future-proof security
- Compliant with NIST's ML-KEM standard
- Pure RTL without hidden CPU or software components
- Optimised architecture with constant-time execution
- Easy system integration with 64-bit interface
- Vendor agnostic FPGA/ASIC implementation
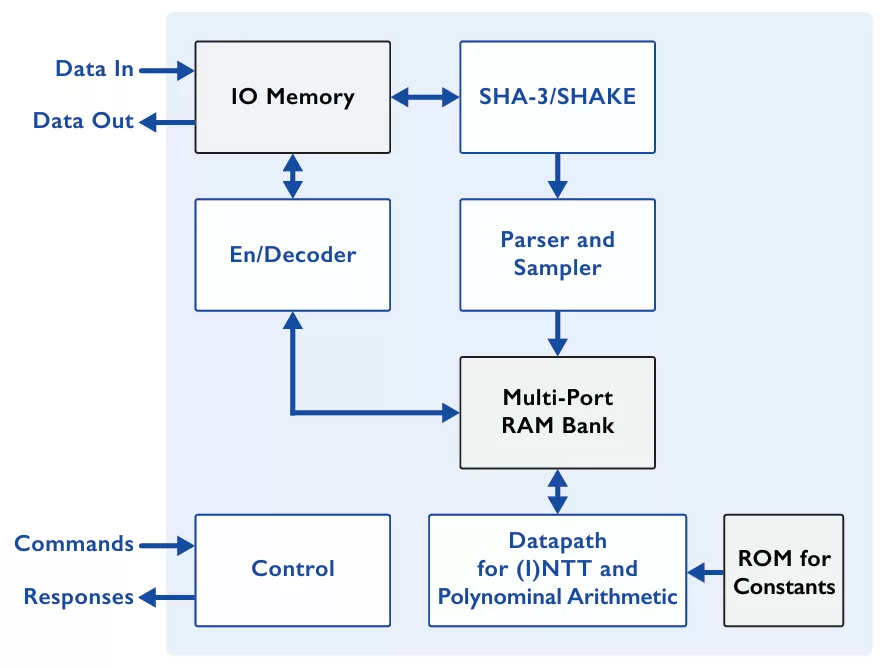
Block Diagram
Benefits
- Supports all security levels
- Minimal resource requirement (less than 10 kLUT)
- Fast performance with thousands of operations/sec
- Easy to integrate
- Several bus interfaces available
- IP core designed in-house at Xiphera
- Technical support by the original designers and cryptographic experts
Applications
- Cryptographic key exchange
- Secure communications
- data storage and transmission
- Quantum-resistant cryptographic protocols
What’s Included?
- Encrypted RTL or source code
- Sample synthesis scripts
- Comprehensive simulation test bench, scripts & guide
- Optional netlist
- Instantiation file
- Detailed datasheet and integration guide
- Please contact sales@xiphera.com for pricing and your preferred delivery method
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Post Quantum IP core
How to design secure SoCs Part IV: Runtime Integrity Protection
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Frequently asked questions about Post-Quantum Cryptography IP cores
What is xQlave® ML-KEM (Kyber) Key Encapsulation Mechanism IP core?
xQlave® ML-KEM (Kyber) Key Encapsulation Mechanism IP core is a Post Quantum IP core from Xiphera Ltd listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.