Provider

Beyond Semiconductor
HQ:
Slovenia
Beyond Semiconductor is a privately held fabless semiconductor IP company supplying embedded processor IP technology for digital consumer, networking, personal entertainment, communications and industrial applications. Beyond Semiconductor believes in technology leadership, excellent value, and superior quality and service.
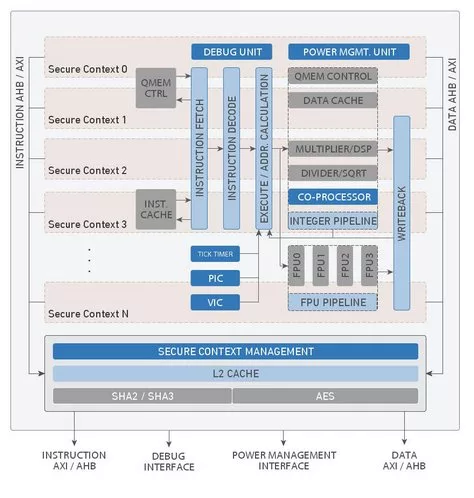
Beyond Semiconductor's comprehensive product offering includes 32-bit embedded RISC/DSP processors, software development tools, peripheral cores and complete reference platforms that enable Licensees to quickly start with product development.
Licensees can develop highly differentiated and competitive system-on-chips (SOCs) by easily customizing the processors to their target applications which can be optimized to achieve the highest performance, smallest size, and lowest power consumption of any 32-bit processor in the same class.
At the heart of Beyond Semiconductor's technology is Beyond Architecture designed with emphasis on performance, simplicity and ease of use, power efficiency and scalability.
We offer products and services in the following areas:
* Scalable range of 32-bit embedded RISC/DSP processors
* Rich set of peripheral cores to go along with the processors
* Complete reference and verification platforms to serve as base designs
* Software development tools
* Operating systems and device drivers
* FPGA/ASIC development and evaluation boards
Committed to helping Licensees achieve their business goals, Beyond Semiconductor aggressively invests in research and development. By partnering closely with our Licensees, Beyond Semiconductor can customize its products to closely match Licensee application requirements.
Beyond Semiconductor products have been successfully implemented by industry leaders like ST Microelectronics, Ericsson, Omnivision, and many others.
Please go to www.beyondsemi.com for more information
Learn more about Security Coprocessor IP core
Security coprocessor ties to PCI Express
This article is divided into two parts. The first part outlines the important features of the IJTAG use model, while the latter part describes a network interface, its architecture, and how it addresses the major challenges of the SoC test.
This paper presents Crypto-RV, a RISC-V co-processor architecture that unifies support for SHA-256, SHA-512, SM3, SHA3-256, SHAKE-128, SHAKE-256 AES-128, HARAKA-256, and HARAKA-512 within a single 64-bit datapath.
With the advent of IoT and increasingly interconnected and autonomous nature of a vehicle’s control modules, there has been an exponential increase in V2V, V2X and inter vehicular communications. This in turn increases the attack surface for hackers which demands state-of-art security features in modern automotive microcontrollers, moreover safety and security go hand in hand.
This article provides an in-depth analysis of the specific PPA challenges introduced by PQC and elucidates how PUF-PQC leverages its unique dualtrack strategy to deliver a robust and flexible Hardware Root of Trust (HRoT) across diverse application scenarios. Furthermore, it demonstrates the integration of Physical Unclonable Function (PUF) with a NIST SP 800-90B compliant True Random Number Generator (TRNG) to serve as critical components of PUFrt (Root of Trust), ensuring the security of post-quantum key generation starting from the entropy source.
For more than 10 years, SHA-1 authentication has been used to effectively protect intellectual property from counterfeiting and illegal copying. As computer technology advances, customers are asking for an even higher level of security.