Root of Trust - Foundational security for SoCs, secure MCU devices and sensors
Designed to be integrated in secure MCUs (microcontrollers), the RT-260 Root of Trust (formerly VaultIP) is a FIPS 140-3 CMVP com…
Overview
Designed to be integrated in secure MCUs (microcontrollers), the RT-260 Root of Trust (formerly VaultIP) is a FIPS 140-3 CMVP compliant hardware core that guards the most sensitive assets on chips and establishes the foundation for platform security.
Featuring a firmware-controlled architecture with dedicated secure memories, the RT-260 hardware Root of Trust provides a variety of cryptographic accelerators including DPA protection for AES, RSA, and ECC. Ideal as a secure services and key manager for MCU (microcontroller) devices, the RT-260 Root of Trust offers the best balance of size and performance available on the market.
The RT-260 offers a series of key security use cases ‘out of the box’, including:
- Secure Boot assist to host CPU(s) and protection of key material
- Secure firmware upgrade management for Host CPU
- Lifecycle management support
- Secure Debug support
- Secure device authentication and identity protection
The RT-260 provides a secure asset store:
- Only the RT-260 can manage, use and access the assets
- The O/S and applications cannot access key values
- Applications request asset use by reference
- Enforces policies for access and use of keys and cryptographic functions
- Key generation, derivation, storage and transport
Features
| Feature | Description | Details |
| FIPS 140-3 | CAVP and CMVP Compliant | Includes CAVP certificates for NIST approved algorithms and TRNG |
| DPA Resistance | Simple and differential power analysis resistant cores | RSA, ECC, AES |
| Cipher Algorithm Support | AES (all key sizes) Optional: ChaCha20, ARIA |
Modes: CBC, CTR, CCM, CMAC, GCM, XTS ARIA Modes: CBC, CTR, CMAC, CCM, GCM |
| Hash Algorithms | SHA-1, SHA-2 Optional: SHA-3 |
SHA-2 224-256-384-512 SHA-3 224-256-384-512 |
| Message Authentication Code Algorithms | HMAC-SHA-1, HMAC-SHA-2 Optional: HMAC-SHA3 |
SHA-2 224-256-384-512 SHA-3 224-256-384-512 |
| AEAD Algorithms | AES-GCM, AES-GMAC, AES-CCM Optional: ChaCha20/Poly1305, ARIA-CCM |
Modes: GCM, GMAC, CCM |
| Signature Generation and Verification | ECDSA EdDSA RSA up to 3096 bits |
NIST P-224, P-256, P-384, P-521 Ed25519 |
| Key Agreement Algorithms | ECDH DH EdDH |
NIST P-224, P-256, P-384, P-521 Up to 3096 bits Curve25519 |
| Key Transport Algorithms | ECIES RSA Wrap/Unwrap (RSA-OAEP) AES-WRAP |
128- and 256-bit strength Up to 3096 bits 128- and 256-bit strength |
| True Random Number Generator | NIST SP800-90A/B/C | NIST ENT certificate |
| Crypto Performance | Cipher/Hash Performance (Gbps) @500MHz | Scalable, ~2 Gbps |
| I/O Bus | AMBA Bus Master/Slave | AXI/AHB Master, AXI/AHB/APB Slave |
| OTP Interface | Interface to 3rd-Party OTP | TCM |
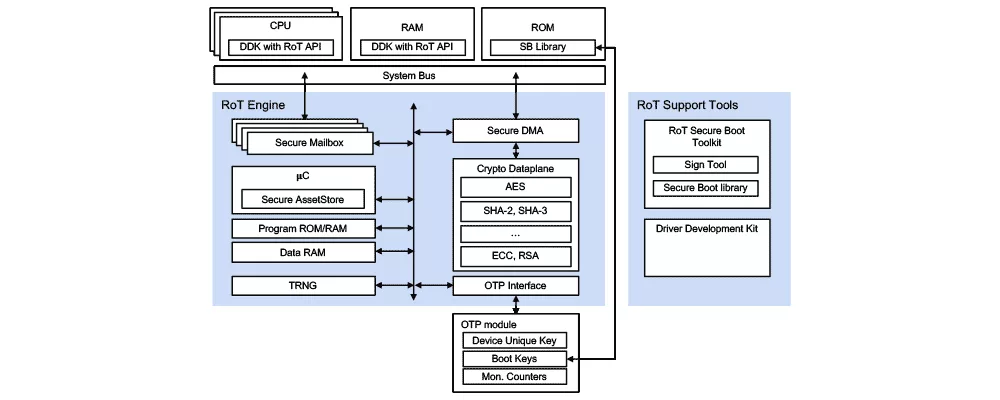
Block Diagram
Benefits
- Side channel attack resistant
- Technology and node independent
- Superior cryptographic protection
- Use with any ASIC or FPGA
Applications
- IoT, IIoT, cloud-connected devices, sensors, gateways
What’s Included?
- Verilog RTL Design database
- Tools and Scripts for synthesis and simulation
- Complete verification test bench and comprehensive set of test vectors
- Complete Documentation Set: Hardware Reference Manual, Programmers Manual, Integration Guide
- Driver Development Kit
Specifications
Identity
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Root Of Trust IP core
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Side-Channel Attacks On Post-Quantum Cryptography
Cryptography Does Not Equal Security
Root of Trust: A Security Essential for Cyber Defense
Frequently asked questions about Root of Trust IP cores
What is Root of Trust - Foundational security for SoCs, secure MCU devices and sensors?
Root of Trust - Foundational security for SoCs, secure MCU devices and sensors is a Root Of Trust IP core from Rambus, Inc. listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.