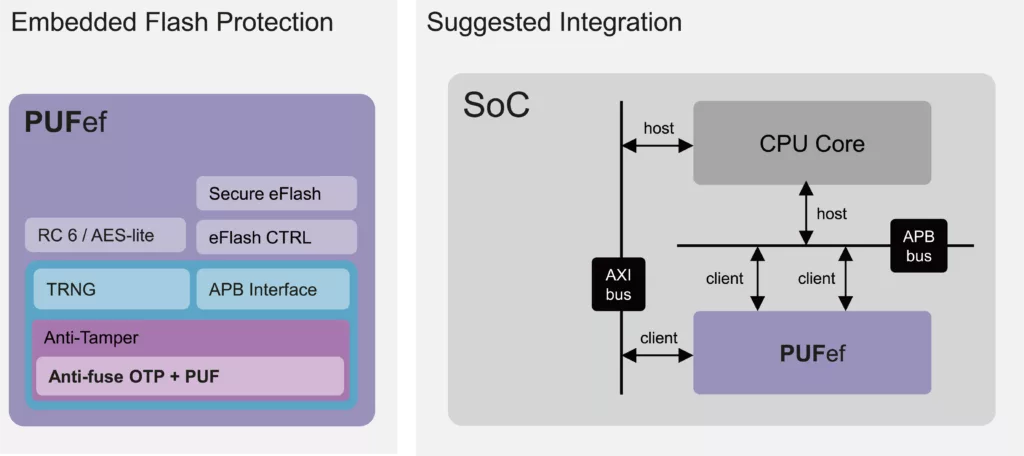
Embedded Flash Protection with Hardware Root of Trust and Lite Crypto Engine
The Flash Protection Series is a suite of enhancements available for PUFcc and PUFrt, extending the Hardware Root of Trust to pro…
Overview
The Flash Protection Series is a suite of enhancements available for PUFcc and PUFrt, extending the Hardware Root of Trust to protect critical assets in the commodity flash. The Flash Protection Series can widen an SoC’s secure boundary based on our highly reliable PUF technology widely available across all major foundries.
Key features
- PUFef is designed to protect embedded Flash with a Hardware Root of Trust and a lite crypto engine of RC6.
- The RC6 provides a comprehensive level of security while also minimizing overall size.
- Before attempting to hack the crypto engine, attackers would first have to destroy the embedded Flash.
Block Diagram
What’s Included?
- Datasheet
- Release Notes
- Integration Guidelines
- Timing .lib File
- LEF
- GDS Phantom File
- Verilog HDL File (Behavior Model)
- Verilog HDL File (FPGA)
- Application Note
- Reference Scripts
- Hard Macro Release Note
- Test Methodology
- Testbench
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Root Of Trust IP core
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Rambus RT-660 Root of Trust IP Achieves FIPS 140-3 Certification
Extending Security IP leadership with FIPS 140-2 CMVP Certification for Root of Trust IP
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Root of Trust IP cores
What is Embedded Flash Protection with Hardware Root of Trust and Lite Crypto Engine?
Embedded Flash Protection with Hardware Root of Trust and Lite Crypto Engine is a Root Of Trust IP core from PUFsecurity listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.