cryptography IP
Filter
Compare
135
IP
from
28
vendors
(1
-
10)
-
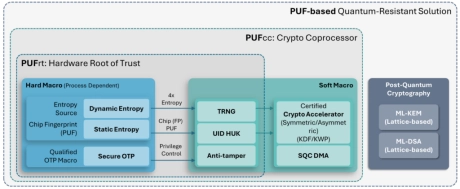
PUF-based Post-Quantum Cryptography (PQC) Solution
- PUFsecurity is proud to pioneer the world’s first PUF-based Post-Quantum Cryptography (PQC) solution, delivering cutting-edge, hardware-level security that sets a new standard.
- Our innovative solution integrates PUF technology with quantum-resistant cryptographic algorithms, ensuring robust key protection and seamless transition to a quantum-secure future.
-
Public-Key Cryptography PKCS IP Core
- Comprehensive implementation in accordance with RSA Laboratories' Public-Key Cryptography Standards (PKCS) series, PKCS #5 v2.0
- Support for SHA256 algorithm
- Technology-independent HDL model
- Simple external interface for easy adaptation
-
High-Performance Hybrid Classical and Post-Quantum Cryptography
- The High-Performance Hybrid Cryptography IP core delivers accelerated support for both classical (RSA, ECC) and post-quantum (ML-KEM, ML-DSA) algorithms in a unified architecture optimized for maximum throughput.
-
Hybrid Classical and Post-Quantum Cryptography
- The Hybrid Cryptography IP core combines traditional asymmetric algorithms—such as RSA and ECC—with post-quantum standards including ML-KEM (Kyber) and ML-DSA (Dilithium)—in a single, efficient hardware module.
-
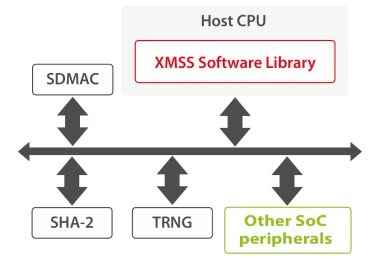
XMSS Post-Quantum Cryptography IP
- XMSS is a Post-Quantum Cryptographic (PQC) algorithm, meaning it is mathematically designed to be robust against a cryptanalytic attack using a quantum computer.
- XMSS is a stateful Hash-Based Signature Scheme that has been recommended by NIST in 2020.
-
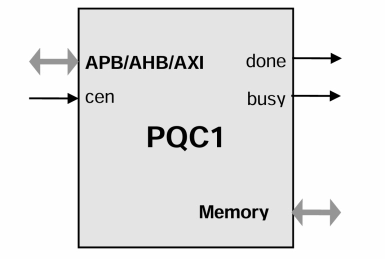
APB Post-Quantum Cryptography Accelerator IP Core
- Implements ML-KEM and ML-DSA post-quantum cryptography digital signature standards. The system interface is an microprocessor slave bus (APB, AHB, AXI options are available).
- The design is fully synchronous and requires only minimal CPU intervention due to internal microprogramming sequencer.
-
Cryptography Software Library
- Symmetric Ciphers
- Hashes
- RSA®
- ECC Prime Curves
- ECC Binary Curves
- Certificates (X.509 v3)
-
Elliptic Curve Cryptography IP
- Supported algorithms:
- Point multiplication
- ECDSA signature generation
- ECDSA signature verification
-
high-performance solution for elliptic curve cryptography
- Supported algorithms:
- Supported Elliptic Curves
- Optional Side Channel Attacks countermeasures
- Input/Output EC point verification
-
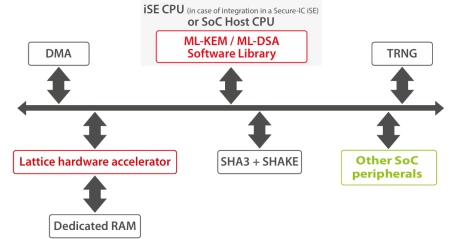
ML-KEM / ML-DSA Post-Quantum Cryptography IP
- ML-KEM (Crystals-Kyber) and ML-DSA (Crystals-Dilithium) are Post-Quantum Cryptographic (PQC) algorithms, meaning they are mathematically designed to be robust against a cryptanalytic attack using a quantum computer.
- Both have been standardized by the NIST in it post-quantum cryptography project.