DPA Countermeasure IP
Filter
Compare
25
IP
from
6
vendors
(1
-
10)
-
Advanced DPA- and FIA-Resistant Software Library
- Ultra-strong side-channel and SIFA protection at high performance
- NIST FIPS-197 compliant
- AES-128/192/256 encryption and decryption
- Tunable protection level
-
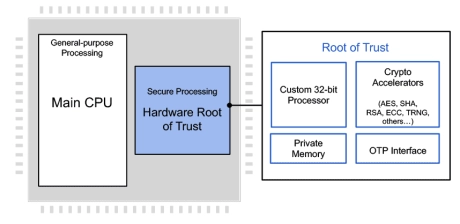
Programmable Root of Trust With DPA and FIA for US Defense
- Custom-designed 32-bit secure RISC-V processor
- Multi-layered security model protects all core components against a wide range of attacks
- Security model includes hierarchical privilege model, secure key management policy, hardware-enforced isolation/access control/protection, error management policy
- State-of-the-art DPA resistance, FIA protection and anti-tamper techniques
-
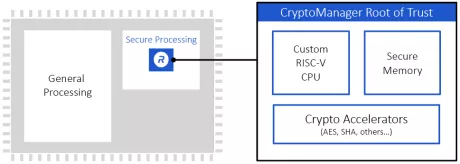
Programmable Root of Trust Family With DPA & Quantum Safe Cryptography
- Hardware Root of Trust employing a custom 32-bit RISC-V processor
- Multi-layered security model provides protection of all components in the core
- NIST CAVP and CMVP compliant for FIPS 140-3 validation
- State-of-the-art anti tamper techniques
- DPA-resistant cryptographic accelerators
- Caliptra Root of Trust for Measurement with DICE and X.509 support
-
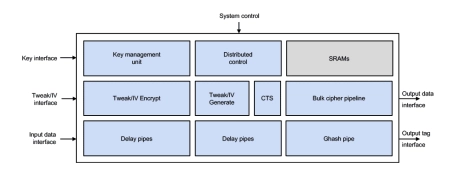
Fast Inline Cipher Engine, AES-XTS/GCM, SM4-XTS/GCM, DPA
- One input word per clock without any backpressure
- Design can switch stream, algorithm, mode, key and/or direction every clock cycle
- GCM: throughput is solely determined by the data width, data alignment and clock frequency
- XTS: block processing rate may be limited by the number of configured tweak encryption & CTS cores; a configuration allowing 1 block/clock is available
-
ChaCha20 DPA Resistant Crypto Accelerator
- Quicken time-to-market using precertified DPA Countermeasures
- Highly secure cryptographic engine primitives
- Extensive validation using the Test Vector Leakage Assessment (TVLA) methodology (revealing no leakage beyond 100 million traces)
- Cores protected against univariate first- and second-order side-channel attacks beyond 1 billion operations
-
AES Authenticated Encryption Accelerator with DPA or with DPA and FIA
- The SCA-resistant AES-IP-3X family of crypto accelerator cores provide semiconductor manufacturers with superior AES cipher acceleration.
- The cores are easily integrated into ASIC/SoC and FPGA devices and offer a high-level of resistance to various Side Channel Attacks like Differential Power Analysis (DPA), and optionally offer detection of Fault Injection Attacks (FIA).
-
DPA Resistant Software Library
- Library implements a very high-security primitives for AES, ECC, RSA, and SHA
- Supported platforms: ARM Cortex-A9, ARM7TDMI, and others
- AES supports 128/192/256-bit encrypt and decrypt
- ECC supports ECDSA/ECDH for NIST prime fields (192/256/384/521)
-
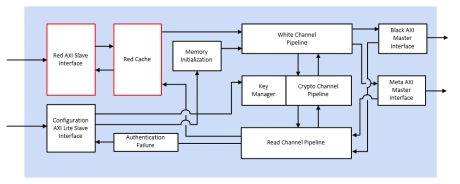
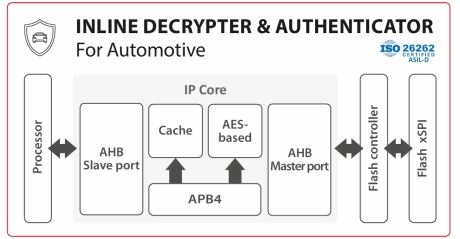
Inline Decrypter & Authenticator IP Core for Automotive
- The Inline Decrypter and Authenticator IP core enables on-the-fly execution of encrypted and signed code from Flash.
- It is used to authenticate and decrypt code located in Flash. In addition it is ISO26262 certified (ASIL-D).
-
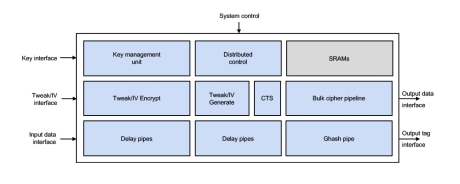
High-speed Inline Cipher Engine
- The ICE-IP-338 data path can be scaled to widths that are multiples of 128 bit to allow a tradeoff between area and performance that best fits the target application.
- Configuration options include or exclude support for CipherText Stealing (CTS), the GCM mode, and the SM4 algorithm and/or Datapath Integrity logic.
- The cryptographic AES and SM4 primitives can be provided with or without side channel attack DPA countermeasures.
-
Inline memory encryption engine, for FPGA
- Performs encryption, decryption and/or authentication using AES Counter Mode (CTR) or Galois Counter Mode (GCM)
- Supports AES key sizes 128 or 256
- Internal key management with NIST-compliant key generation
- Encrypt memory space into user-defined vaults, each with a unique key
- Compatible with AMBA AXI4 interface
- Supports hard or soft memory controllers in Xilinx FPGA and SoC devices
- Supports multiprocessor systems