Importance Of Hardware Security Verification In Pre-Silicon Design
Today’s semiconductor chips run cloud infrastructure, automotive controllers, industrial robots, and edge AI processors, so effectively the entire technology market. Engineers must now ensure that silicon itself defends against attacks, protects embedded secrets, and complies with increasingly stringent global security standards, such as ISO/SAE 21434 and the EU Cyber Resilience Act. Regulators, partners, customers, hyperscalers, and end-product developers now expect proof that security was built in during the architecture phase. Every transistor now carries a burden of trust that extends throughout the entire development process. This requires a systematic approach to security throughout the pre-silicon development cycle, using verification to uncover weaknesses and evaluate effectiveness.
 Security coverage provides a structured, measurable method for evaluating functionality and protections, identifying vulnerabilities, and verifying processes. This enables engineering teams to assess how thoroughly security controls are exercised and to detect potential gaps throughout the design lifecycle. The real challenge is knowing with confidence that defined assets, constraints, and protection boundaries are correctly enforced and remain effective.
Security coverage provides a structured, measurable method for evaluating functionality and protections, identifying vulnerabilities, and verifying processes. This enables engineering teams to assess how thoroughly security controls are exercised and to detect potential gaps throughout the design lifecycle. The real challenge is knowing with confidence that defined assets, constraints, and protection boundaries are correctly enforced and remain effective.
Two necessary pillars
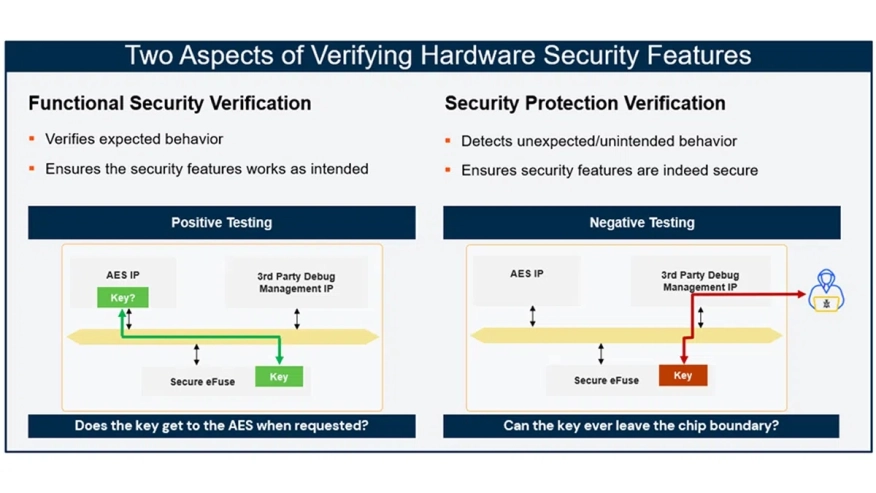
Hardware security comes down to two core pillars. Functional security verification confirms correctness, and security protection verification establishes robustness.
The functional security verification pillar ensures that security functionality behaves correctly under defined operating conditions and expected use cases. It uses known methods such as simulation, assertions, and formal analysis.
To read the full article on Semiconductor Engineering, click here.
Related Semiconductor IP
- Smart Network-on-Chip (NoC) IP
- FlexNoC 5 Interconnect IP
- FlexNoC Functional Safety (FuSa) Option helps meet up to ISO 26262 ASIL B and D requirements against random hardware faults.
- Network-on-Chip (NoC)
- NoC Verification IP
Related Blogs
- Cryptographic Modules Provide Critical Security in a Unified and Isolated Hardware Solution
- Why Hardware Security Is Just as Critical as Software Security in Modern Systems
- Programmable Hardware Delivers 10,000X Improvement in Verification Speed over Software for Forward Error Correction
- Rambus and the OCP: Tackling Cloud Data Security with a Hardware Root of Trust
Latest Blogs
- A Bench-to-In-Field Telemetry Platform for Datacenter Power Management
- IDS-Verify™: From Specification to Sign-Off – Automated CSR, Hardware Software Interface and CPU-Peripheral Interface Verification
- RISC-V and GPU Synergy in Practice: A Path Towards High-Performance SoCs from SpacemiT K3
- EDA AI Agents: Intelligent Automation in Semiconductor & PCB Design
- Why Security Can't Exist Without Trust
