PUF-based Post-Quantum Cryptography (PQC) Solution
As quantum computing advances at an unprecedented pace, traditional cryptographic systems are encountering new challenges.
Overview
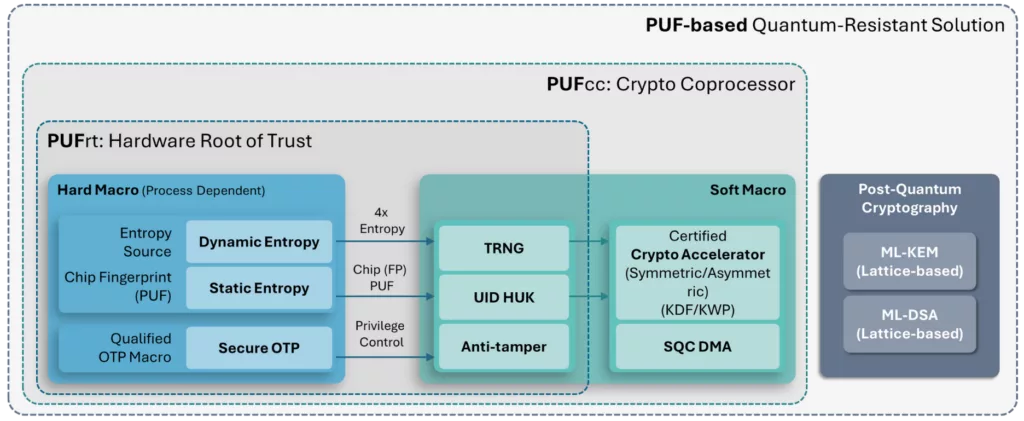
As quantum computing advances at an unprecedented pace, traditional cryptographic systems are encountering new challenges. PUFsecurity is proud to pioneer the world’s first PUF-based Post-Quantum Cryptography (PQC) solution, delivering cutting-edge, hardware-level security that sets a new standard. Our innovative solution integrates PUF technology with quantum-resistant cryptographic algorithms, ensuring robust key protection and seamless transition to a quantum-secure future. This approach provides backward compatibility with existing security infrastructure while strengthening resilience against quantum threats—safeguarding your data, devices, and intellectual property for the long term.
Key features
- FIPS 203 (ML-KEM): The Module-Lattice-Based Key Encapsulation Mechanism Standard, built on the CRYSTALS-Kyber mechanism, ensures secure key exchange with resistance to quantum attacks.
- FIPS 204 (ML-DSA): The Module-Lattice-Based Digital Signature Standard, built on the CRYSTALS-Dilithium signature scheme, provides uncompromised digital signature integrity.
- NTT (Polynomial Arithmetic) and SHA-3/SHAKE Hardware Acceleration
Block Diagram
Applications
- Anti-quantum asymmetric key pairs are generated by PUF-based PQC engines.
- Static random seeds are derived by innate NeoPUF in PUFrt without HUK injection; while dynamic random seeds are provided by a high-performance PUF-based TRNG in PUFrt.
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Post Quantum IP core
How to design secure SoCs Part IV: Runtime Integrity Protection
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Frequently asked questions about Post-Quantum Cryptography IP cores
What is PUF-based Post-Quantum Cryptography (PQC) Solution?
PUF-based Post-Quantum Cryptography (PQC) Solution is a Post Quantum IP core from PUFsecurity listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.