ML-KEM Key Encapsulation & ML-DSA Digital Signature Engine
The KiviPQC™-Box is a hardware accelerator for post-quantum cryptographic operations.
Overview
The KiviPQC™-Box is a hardware accelerator for post-quantum cryptographic operations. It implements both the Module Lattice-based Key Encapsulation Mechanism (ML-KEM) and the Module Lattice-based Digital Signature Algorithm (ML-DSA), standardized by NIST in FIPS 203 and FIPS 204, respectively. The ML-KEM mechanism realizes the appropriate procedures for securely exchanging a shared secret key between two parties that communicate over a public channel using a defined set of rules and parameters. The ML-DSA mechanism concerns the appropriate procedures for securely generating a private/public key pair, digitally signing a message or a data block, and performing digital signature verification.
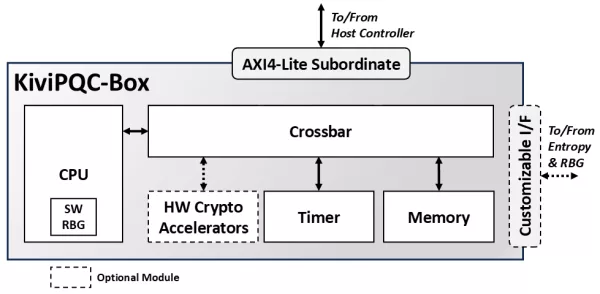
The engine offers multi-mode operation to support all the above procedures. It supports all parameter sets for ML-KEM (ML-KEM-512, ML-KEM-768, ML-KEM-1024) and for ML-DSA (ML-DSA-44, ML-DSA-65, ML-DSA-87). It is based on a RISC-V-like SoC topology, including a 32-bit RISC-V based processor. Designed for straightforward integration, the communication with the host is accomplished via an AMBA® AXI4-Lite Subordinate port.
Two versions are available: a Fast (F) and a Tiny (T) version. The Fast (F) includes hardware crypto accelerators, a hardware timer module, and a crossbar interconnect module for internal data routing. The Tiny (T) version is a more compact architecture, targeting low area, with no hardware crypto accelerators. Both versions are currently offered with a software implementation of a Random Byte Generator (RBG), however, they are able to be integrated with an external (third-party) entropy source and RBG, via a fully customized interface, depending on the entropy/RBG selection.
The KiviPQC™-Box provides hardware acceleration for computationally intensive operations while maintaining a small footprint and can be integrated into any system-on-chip (SoC) for ASIC or FPGA implementation. Beyond that, it combines a minimal attack surface with modest resource requirements for future-proof and quantum-safe systems.
Key features
NIST FIPS Compliant
- Module Lattice-based Key Encapsulation Mechanism (ML-KEM)
- NIST FIPS 203
- All three ML-KEM parameter sets (512 / 768 / 1024)
- Module Lattice-based Digital Signature Algorithm (ML-DSA)
- NIST FIPS 204
- All three ML-DSA parameter sets (44 / 65 / 87)
Versions
- Fast (F): Enhanced performance, with balanced area
- Tiny (T): Compact architecture, targeting low area
Enhanced Security
- Self-contained engine with a minimal attack surface
- Protection against timing-based side channel attacks
Resource-efficient Acceleration
- Hardware offloading and acceleration of time-consuming PQC operations
- 600MHz, with 83k eq. gates in modern ASICs for Fast version
- Sharing resources for two PQC operations (multi-mode)
- 31k or less eq. gates in modern ASICs for Tiny version
Straightforward SoC Integration
- Lightweight, simple-control AMBA® AXI4 Interface
- Re-usable design, LINT-clean
Block Diagram
Applications
- The KiviPQC™-Box is a quantum-safe solution for shared secret key exchange and digital signature mechanism, when communicating over a public channel. During the key sharing, the client generates a decapsulation key and an encapsulation key, keeps the first as private and sends the second as public to the server. The server generates a copy of the shared key and an associated ciphertext using the client’s encapsulation key, and sends it to the client. Finally, the client generates a copy of the same shared key using the ciphertext received from the server and the kept private decapsulation key.
- Concerning the digital signature mechanism, the signatory generates a private/public key pair. Next, the signatory uses the private key to sign a message (and optionally a context string). Then, the verifier employs the public key (and optionally the context string) to verify the signature.
- Supporting ML-KEM, the KiviPQC™-Box protects sensitive data with long-term integrity in public-key infrastructure and cloud. It strengthens safety-critical networks, IoT device communication, and secure key handling in HSMs and TPMs. It also supports protocols such as MACsec MKA for Ethernet, IKEv2 for VPNs, and authentication in edge computing.
- Beyond the above, by employing ML-DSA — which will replace RSA and ECDSA across the ecosystem wherever digital signatures are required — the engine is suited for SoCs that need long-term protection against quantum attacks in software and firmware signing for critical systems and IoT devices, secure communication and messaging protocols, blockchain transaction signing, and digital identity solutions.
What’s Included?
The core is available in RTL (System Verilog) source code.
Its deliverable package includes the following:
- Self-checking HDL testbench
- Hardware Abstraction Layer (HAL) and driver for the application processor
- Sample simulation & synthesis scripts
- User documentation
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Post Quantum IP core
How to design secure SoCs Part IV: Runtime Integrity Protection
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Frequently asked questions about Post-Quantum Cryptography IP cores
What is ML-KEM Key Encapsulation & ML-DSA Digital Signature Engine?
ML-KEM Key Encapsulation & ML-DSA Digital Signature Engine is a Post Quantum IP core from CAST listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.