APB Post-Quantum Cryptography Accelerator IP Core
Implements ML-KEM and ML-DSA post-quantum cryptography digital signature standards.
Overview
Implements ML-KEM and ML-DSA post-quantum cryptography digital signature standards. The system interface is an microprocessor slave bus (APB, AHB, AXI options are available).
The design is fully synchronous and requires only minimal CPU intervention due to internal microprogramming sequencer.
The core contains three accelerators:
- The number theoretic transform NTT accelerator also capable of other vector polynomial operations
- The FIPS-202 accelerator supporting SHA-3, SHAKE128 and SHAKE256 algorithms
- The packing/unpacking accelerator that handles the key and signature formats defined by FIPS-203 and FIPS-204
True random number generator (needed for key generation or randomization of signing) is not included. The true random generator IP core TRNG1 can be used for that purpose.
Performance
| Operation | Category | Performance, ops/sec |
|---|---|---|
| ML-DSA signature generation¹ | 2 | 15,000 |
| 3 | 10,000 | |
| 5 | 7,000 | |
| ML-DSA key generation | 2 | 30,000 |
| 3 | 20,000 | |
| 5 | 12,000 | |
| ML-DSA signature verification | 2 | 33,000 |
| 3 | 21,000 | |
| 5 | 13,000 | |
| ML-KEM key generation | 1 | 95,000 |
| 3 | 55,000 | |
| 5 | 35,000 | |
| ML-KEM encryption | 1 | 65,000 |
| 3 | 40,000 | |
| 5 | 28,000 | |
| ML-KEM decryption | 1 | 230,000 |
| 3 | 180,000 | |
| 5 | 145,000 |
Key features
- Support for ML-KEM(FIPS-203, Kyber) and ML-DSA algorithms(FIPS-204, Dilithium) with built-in NTT and SHAKE128/SHAKE256/SHA-3 engines accessible externally
- Self-contained, except for the single-port external RAM banks
- Uses 32-bit-wide APB Lite interface
- Supports all MS-DSA algorithms defined in FIPS-204 (from Category 2 ML-DSA-44, Category 3 ML-DSA-65, Category 5 ML-DSA-87) and all FIPS-203 ML-KEM algorithms (ML-KEM-512, ML-KEM-768, and ML-KEM- 1024).
- An SDK is provided for software development with support for ML-DSA (key generation, signing, and signature verification) and ML-KEM (key generation, key encapsulation, and key decapsulation).
- High clock rate. Timing closure at 1 GHz clock in ASIC with easy, higher frequencies are possible.
- Deliverables include Verilog test bench and test vectors
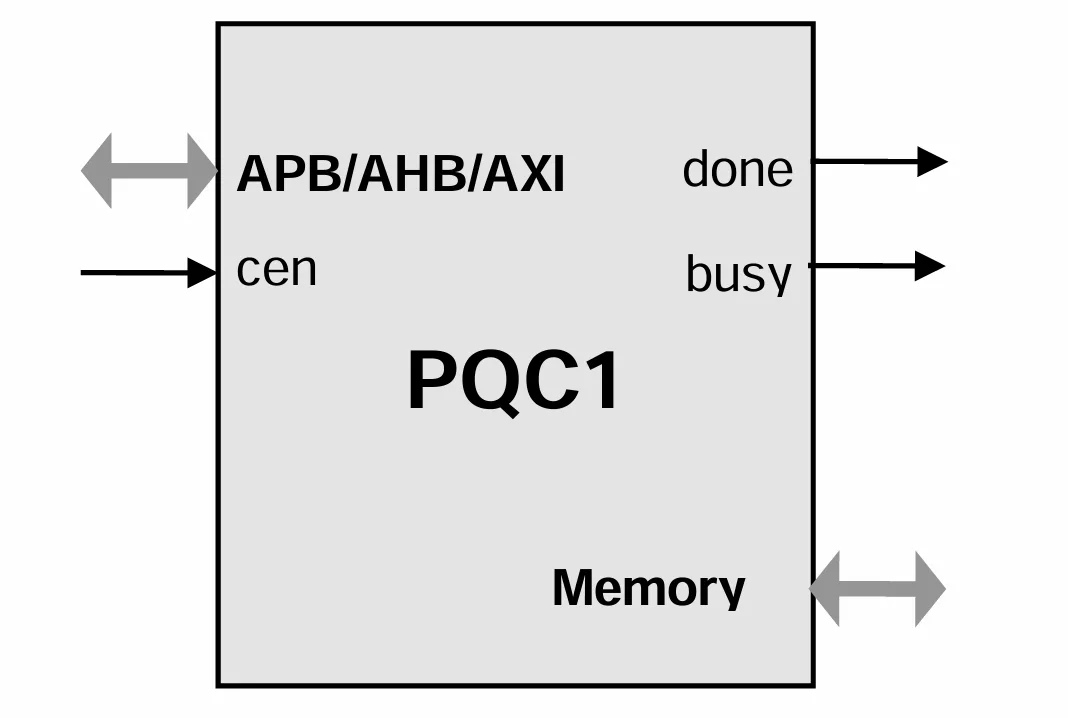
Block Diagram
Applications
- Post-Quantum cryptgraphy
What’s Included?
- Synthesizable Verilog RTL source code
- Test bench (self-checking)
- Test vectors
- Expected results
- Software Development Kit (SDK)
- User Documentation
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Post Quantum IP core
How to design secure SoCs Part IV: Runtime Integrity Protection
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Frequently asked questions about Post-Quantum Cryptography IP cores
What is APB Post-Quantum Cryptography Accelerator IP Core?
APB Post-Quantum Cryptography Accelerator IP Core is a Post Quantum IP core from IP Cores, Inc. listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.