Crypto Coprocessor with integrated Post-Quantum Cryptography IPs
The Crypto Coprocessors are a hardware IP core platform that accelerates cryptographic operations in System-on-Chip (SoC) environ…
Overview
The Crypto Coprocessors are a hardware IP core platform that accelerates cryptographic operations in System-on-Chip (SoC) environment on FPGA or ASIC.
Symmetric operations are offloaded very efficiently as it has a built-in scatter/gather DMA. The coprocessors can be used to accelerate/offload IPsec, VPN, TLS/SSL, disk encryption, or any custom application requiring cryptography algorithms.
Post-Quantum Cryptographic algorithms are including in the solutions to accelerate/offload security operations based on XMSS for FW verification, or on Crystals Kyber for secure Key Exchange, or also on Crystals Dilithium for Digital Signature.
Key features
- Scalable architecture and crypto engines for optimal performance/resource usage
- Configurable for perfect application fit
- 100% CPU offload with low latency and high throughput
- DPA countermeasures Full software/driver support
- Easy integration with AXI interfaces
- FIPS 140-2 validated: CAVP #C742
- Embedded DMA to optimize memory access
- Embedded TRNG for random seed generation
- Supported Traditional Cryptographic algorithms:
- AES/SM4
- SHA1/SHA2/SHA3/SM3 with HMAC
- RSA/ECC/SM2
- Chacha20-Poly1305
- ARIA
- Kasumi
- Snow3G
- ZUC
- DES
- Supported Post-Quantum Cryptographic algorithms :
- Crystals-Kyber/Crystals-Dilithium
- XMSS
- LMS
- SPHINCS+
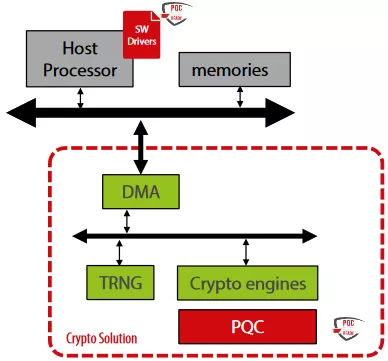
Block Diagram
Benefits
- The Coprocessors platform integrates your desired selection of our cryptographic IP cores (including our TRNG solutions), additional interfacing, DMA and software layers providing a complete solution.
- Depending on needs, the solution can be configured to embed only accelerators required for PQC algorithms, or a hybrid solution embedding both PQC algorithms and traditional cryptography.
Applications
- Secure Communication (TLS, IPSec, BLE, Zigbee, others…)
- Secure boot support
- Secure storage
What’s Included?
- Netlist or RTL
- SW drivers (Linux) & OpenSSL Scripts for implementations
- Self-checking RTL test-bench based on FIPS vectors
- Documentation
Specifications
Identity
Provider

Learn more about Post Quantum IP core
How to design secure SoCs Part IV: Runtime Integrity Protection
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Frequently asked questions about Post-Quantum Cryptography IP cores
What is Crypto Coprocessor with integrated Post-Quantum Cryptography IPs?
Crypto Coprocessor with integrated Post-Quantum Cryptography IPs is a Post Quantum IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.