TLS - Validates TLS protocols to ensure secure, encrypted data transmission
TLS Verification IP (VIP) ensures secure communication by validating TLS protocol implementations.
Overview
TLS Verification IP (VIP) ensures secure communication by validating TLS protocol implementations. It simulates handshake processes, tests encryption, and verifies data integrity to protect against cyber threats during data transmission.
This product finds application in web browsing, email security, VPNs, cloud services, mobile apps, and more. It safeguards sensitive data across various platforms, ensuring end-to-end encryption and robust protection in diverse network environments
Key features
- Protocol Compliance Testing: Ensures that the system adheres to the latest TLS protocol specifications, following industry standards for secure communication.
- End-to-End Security: Validates that data exchanged between the client and server is securely encrypted, protecting it from interception and tampering.
- Cipher Suite Verification: Verifies that only strong and current cipher suites are used for encryption, preventing the use of outdated or weak algorithms.
- Handshake Process Simulation: Simulates the entire TLS handshake process, including key exchange and authentication, ensuring a secure session setup.
- Session Resumption: Validates that previously established sessions can be resumed securely, improving performance without compromising encryption.
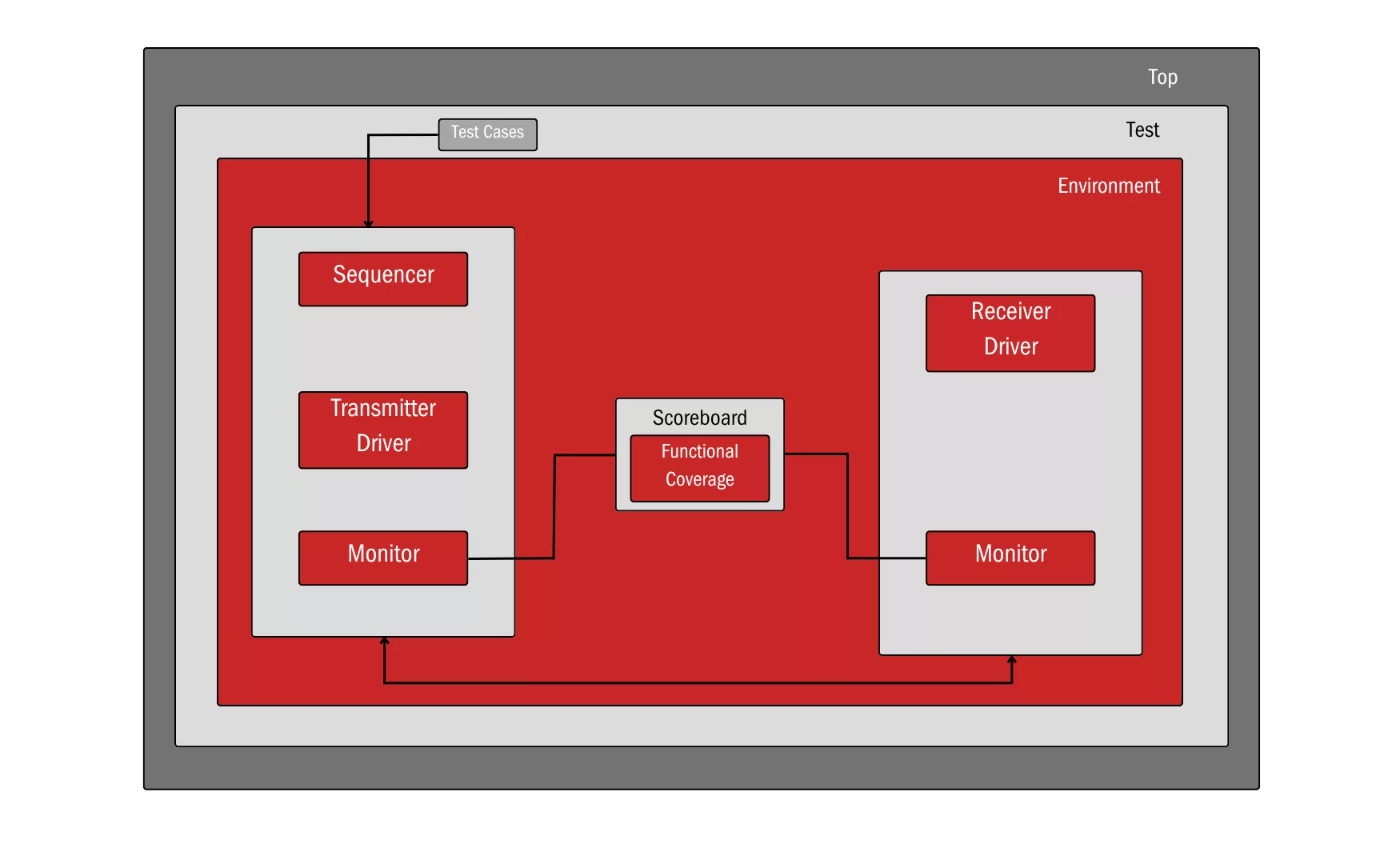
Block Diagram
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about IPsec / TLS IP core
ML-KEM explained: Quantum-safe Key Exchange for secure embedded Hardware
How to design secure SoCs, Part V: Data Protection and Encryption
Cryptography Does Not Equal Security
MACsec for Deterministic Ethernet applications
Satellite communications are no longer as secure as assumed
Frequently asked questions about IPsec / TLS IP cores
What is TLS - Validates TLS protocols to ensure secure, encrypted data transmission?
TLS - Validates TLS protocols to ensure secure, encrypted data transmission is a IPsec / TLS IP core from XtremeSilica listed on Semi IP Hub.
How should engineers evaluate this IPsec / TLS?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this IPsec / TLS IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.