SHA-3 Secure Hash Crypto Engine
The SHA-3 is a high-throughput, area-efficient hardware accelerator for the SHA-3 cryptographic hashing functions, compliant to N…
Overview
The SHA-3 is a high-throughput, area-efficient hardware accelerator for the SHA-3 cryptographic hashing functions, compliant to NIST’s FIPS 180-4 and FIPS 202 standards.
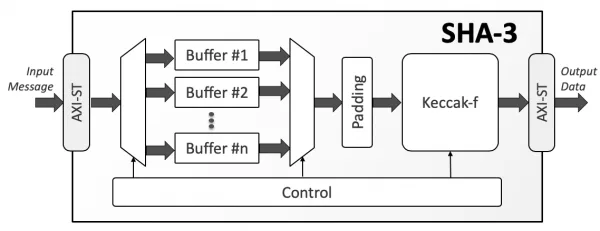
The accelerator core requires no assistance from a host processor and uses standard AMBA® AXI4-Stream interfaces for input and output data. An AXI4-Stream to AXI4 Memory Mapped bridge, with or without DMA capabilities, can be used with the core and is separately available from CAST. A single instance of the core implements all fixed-length and extendable-output hash functions. The cryptographic function, the length of the extendable output function (up to 2GB) is chosen at run time via AXI4-Stream side-band signals and can be different for every input message.
The SHA-3 core is also highly configurable at synthesis time, to ease integration in systems with different requirements. The data-bus width of the input and output interfaces is configurable at synthesis time. The number of SHA-3 permutation rounds per clock cycle is also configurable at synthesis time, allowing users to trade throughput for silicon resources. Under its minimum configuration of one permutation per cycle, the core processes 50 bits per cycle depending on the hashing function. Its throughput can scale by implementing 2, 3, or 4 permutations per cycle respectively, enabling throughputs in excess of 100Gbps in modern ASIC technologies.
The core is designed for ease of use and integration and adheres to industry-best coding and verification practices. Technology mapping, and timing closure are trouble-free, as the core contains no multi-cycle or false paths, and uses only ris-ing-edge-triggered D-type flip-flops, no tri-states, and a single-clock/reset domain.
The SHA-3 IP core can be used to ensure data integrity and/or verify authentication in a wide range of applications including IP-sec and TLS/SSL protocol engines, secure boot engines, encrypted data storage, e-commerce, and financial transaction systems.
Key features
- Standards Support
- FIPS 202: SHA-3 - Permutation-Based Hash and Extendable-Output Function
- FIPS 180-4: Secure Hash Functions (limited to SHA-3 use)
- All four fixed-length SHA-3 Hash Functions:
- SHA3-224
- SHA3-256
- SHA3-384
- SHA3-512
- Both SHA-3 Extendable Output Functions (XOF):
- SHAKE-128
- SHAKE-256
- NIST-Validated
- Performance
- User-selectable (1 to 4) permutation rounds per clock cycle, resulting in a throughput of:
- Up to 50 Mbits/MHz for one permutation per cycle
- Up to 150 Mbits/MHz for four permutations per cycle
- Intelligent buffers management optionally allows receiving new input while processing the previous message
- Optional dynamic control of the number of permutation rounds
- User-selectable (1 to 4) permutation rounds per clock cycle, resulting in a throughput of:
- Interfaces
- AMBA® AXI4-Stream
- Fully autonomous operation
- Requires no assistance from the host processor
- Automatic padding insertion
- Configuration Options
- Hashing function (bit-rate, capacity, number of permutation rounds)
- Input & output bus bit-width
- Number of input buffers
- Number of permutations per cycle
- Enable/disable dynamic control of permutation rounds
- Deliverables
- Verilog RTL source code or targeted FPGA netlist
- Integration Test-Bench
- Simulation & synthesis scripts
- Bit Accurate C Model
- User documentation
Block Diagram
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Hash / MAC IP core
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Data-in-transit Protection for Application Processors
Frequently asked questions about Hash / MAC IP cores
What is SHA-3 Secure Hash Crypto Engine?
SHA-3 Secure Hash Crypto Engine is a Hash / MAC IP core from CAST listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.