SHA3 Cryptographic Hash Cores
The SHA cores provide implementation of cryptographic hashes “Keccak” SHA-3 (cores SHA3-224, SHA3-256, SHA3-384 and SHA3-512) and…
Overview
The SHA cores provide implementation of cryptographic hashes “Keccak” SHA-3 (cores SHA3-224, SHA3-256, SHA3-384 and SHA3-512) and (optionally) the corresponding hash-based HMAC, KMAC, and XOF (SHAKE) functions
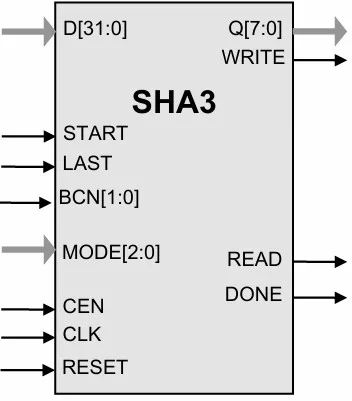
The cores utilize “flow-through” design that can be easily included into the data path of a communication system or connected to a microprocessor: the core reads the data via the D input and outputs the hash result via its Q output. Data bus widths for both D and Q are parameterized.
The design is fully synchronous and is available in both source and netlist form.
Function Description
The SHA-3 algorithms process data in block of different size that depends on the particular algorithm:
| Hash | Block size("bitrate") |
|---|---|
| SHA3-224 | 1152 |
| SHA3-384 | 832 |
| SHA3-256 | 1088 |
| SHA3-512 | 576 |
The Secure Hash Standard (SHA-3) is a message digest standard as defined in the FIPS-202 publication
http://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.202.pdf .
The core is designed for flow-through operation. The input data can contain any number of bytes up to 229 (data padding is performed inside the core). The output data is the 224/256/384/512-bit hash or HMAC value.
Key features
- Completely self-contained; does not require external memory
- SHA3-224, SHA3-256, SHA3-384, and SHA3-512 support SHA-3 algorithms per FIPS 202.
- SHAKE128 / SHAKE256 XOF support is included.
- Flow-through design; flexible data bus width
- Test bench provided
Block Diagram
Applications
- Post-quantum cryptography(PQC)
- Message digest calculation
- Digital signature (DSA) algorithm of the Digital Signature Standard (DSS) per FIPS-186
- Key derivation function (HKDF per RFC RFC 9688)
- KMAC128 or KMAC256 as defined in Section 4.4 of NIST.SP.800-108r1-upd1
- Security protocols, including
- S/MIME (PKCS #1, RFC 9688)
- IPSec
What’s Included?
- Synthesizable Verilog RTL source code
- Test bench (self-checking)
- vectors for testbenches
- Expected results
- User Documentation
Specifications
Identity
Security
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Hash / MAC IP core
Embedded Security explained: Cryptographic Hash Functions
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is SHA3 Cryptographic Hash Cores?
SHA3 Cryptographic Hash Cores is a Hash / MAC IP core from IP Cores, Inc. listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.