256-bit SHA Secure Hash Crypto Engine
The SHA-256 encryption IP core is a fully compliant implementation of the Message Digest Algorithm SHA-256.
Overview
The SHA-256 encryption IP core is a fully compliant implementation of the Message Digest Algorithm SHA-256. It computes a 256-bit message digest for messages of up to (264 – 1) bits.
Developed for easy reuse in ASIC and FPGA applications, the SHA-256 is available optimized for several technologies with competitive utilization and performance characteristics. Support for AMBA bus interfaces and integration with an external DMA are available as options.
The SHA-256 can be used in various applications for ensuring data integrity, and authenticity. Some examples are on-chip communication, electronic fund transfers, digital signatures, password storage, blockchain technology and data backup.
Key features
- NIST-Validated SHA-256 implementation compliant to FIPS 180-4
- Input length up to (264 – 1) bits
- High throughput:
- 65 clock cycles per 512-bit input block
- Over 10Gbps on modern ASIC technologies
- Throughput scaling with multiple clock instances.
- Small Silicon footprint: 15k-20k Gates
- Easy integration & implementation
- Fully synchronous, uses only the rising clock-edge, single-clock domain, no false or multicycle timing paths, scan-ready, LINT-clean, reusable design
- Simple input and output interfaces optionally bridged to AMBA™ interfaces or integrated with a DMA engine.
- Available in VHDL or Verilog source code format, or as a targeted FPGA netlist
- Complete deliverables include test benches, C model, and test vector generator
- Multiple times production-proven in ASIC and FPGA designs
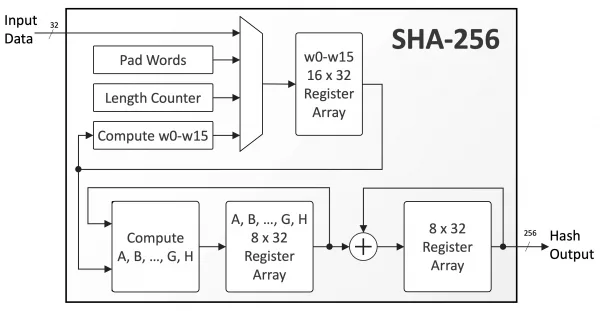
Block Diagram
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Hash / MAC IP core
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Data-in-transit Protection for Application Processors
Frequently asked questions about Hash / MAC IP cores
What is 256-bit SHA Secure Hash Crypto Engine?
256-bit SHA Secure Hash Crypto Engine is a Hash / MAC IP core from CAST listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.