SHA3 Secure Hash Algorithm IP Core (224/256/384/512)
The KiviHash-SHA-3 (secure hash algorithms) is a hardware accelerator for cryptographic hashing functions.
Overview
The KiviHash-SHA-3 (secure hash algorithms) is a hardware accelerator for cryptographic hashing functions. It is an area efficient and high throughput design and compliant to NIST’s FIPS 202 standard. It supports all SHA-3 hash functions (SHA-3-224, SHA-3-256, SHA-3-384 and SHA-3-512) as well as extendable output functions (XOF), SHAKE-128 and SHAKE-256. It provides full protection against time-based side channel attacks (SCA). Automatic byte padding is included. It operates in a single clock domain and has been extensively verified.
Key features
- NIST FIPS 202 compliant
- Supports cryptographic hashing for SHA-3 in 224/256/384/512 mode
- Supports cryptographic hashing for Keccak in 224/256/384/512 mode
- Extendable-Output Functions for SHAKE 128/256
- AMBA® AXI4-Lite Interface
- Fully synchronous design
- HAL and software driver (C-code, platform independent)
- Platform agnostic design for any FPGA
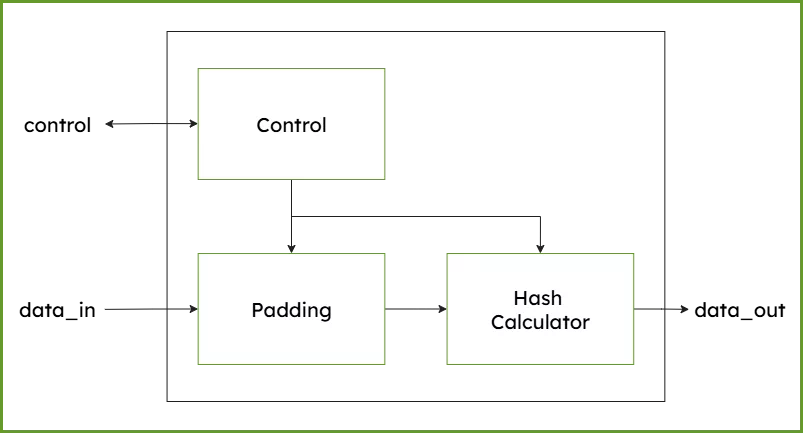
Block Diagram
Benefits
Easy integration
- AMBA® AXI4 lite Interface
- Platform agnostic C source code HAL, API and software driver
- Software examples included
- Software user guide
- Integration examples
- Comprehensive documentation
Test and Verification
- NIST CAVS test vectors for SHA3 hash functions
- NIST CAVS test vectors for SHA3 XOF functions
- Extended verification through simulation
- FPGA integration and implementation tests
- Unity tests for driver and whole IP Core
Applications
The SHA-3 IP core offers a versatile solution for maintaining data integrity and verifying authentication across various applications.
- Firmware Updates: Detecting tampered or corrupted update packages
- FPGA bitstreams: Ensuring only trusted configurations are loaded
- Communication protocols: TLS, IPsec, MAC-based authentication
- External memory integrity: Protecting stored data in flash or external RAM
What’s Included?
- System Verilog RTL Source Code
- Testbenches
- Integration examples
- Software example source code
- Documentation
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Security
Provider

Learn more about Hash / MAC IP core
The Challenge of Automotive Hardware Security Deployment
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is SHA3 Secure Hash Algorithm IP Core (224/256/384/512)?
SHA3 Secure Hash Algorithm IP Core (224/256/384/512) is a Hash / MAC IP core from KiviCore listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.