HKDF/HMAC/SHA-384, SHA-384 IP Core with Extended Functionalities
XIP3323B is a versatile Intellectual Property (IP) core designed for SHA-384 cryptographic hash function with extended support fo…
Overview
XIP3323B is a versatile Intellectual Property (IP) core designed for SHA-384 cryptographic hash function with extended support for HMAC message authentication code and HKDF key derivation function that are based on using SHA-384. SHA-384 is one of the most commonly used hash functions and is used in numerous cryptographic applications. XIP3323B offers a good balance between performance and resource requirements.
XIP3323B has been designed for easy integration with FPGA- and ASIC-based designs in a vendor-agnostic design methodology, and the functionality of XIP3323B does not rely on any FPGA manufacturer-specific features.
XIP3323B has also been successfully validated in the CAVP (Cryptographic Algorithm Validation Program) by NIST (National Institute for Standards and Technology).
Key features
- Versatility: XIP3323B supports the widely used cryptographic hash function SHA-384. It also has native support for commonly used message authentication code (HMAC) based on SHA-384 and key derivation function (HKDF) based on HMAC. This allows using XIP3323B for multiple cryptographic functions - for example, TLS 1.3 - more easily and efficiently than an IP core that supports only SHA-384.
- Constant Latency: The execution time of XIP3323B is independent of the message and key values (apart from message length), and consequently provides protection against timing-based side-channel attacks.
- Performance: XIP3323B provides high performance and reaches hashing speeds of several hundreds of Mbps.
- Compact Size: XIP3323B has compact size (for example, 2481 ALMs and 6 M20K blocks in Intel Cyclone 10 GX family) permitting integration into resource constrained FPGA designs.
- Standard Compliance: XIP3323B is compliant with NIST FIPS 180-4 Secure Hash Standard (SHS), FIPS 198-1 The Keyed-Hash Message Authentication Code (HMAC), and RFC 5869 HMAC-based Extract-and-Expand Key Derivation Function (HKDF). Consequently, XIP3323B can be used in multiple cryptographic applications.
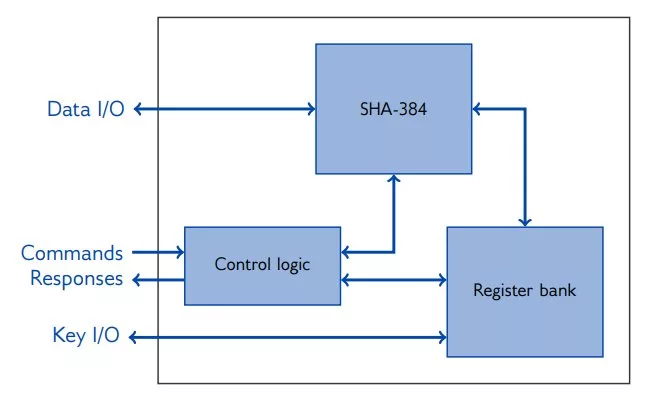
Block Diagram
Benefits
- Fully digital design
- Portable to any ASIC or FPGA technology
- Fully standard compliant
- Easy to integrate
- Several bus interfaces available
- IP core designed in-house at Xiphera
- Technical support by the original designers and cryptographic experts
- CAVP validated
Applications
- XIP3323B supports four main functionalities:
- SHA-384: Computes a SHA-256 hash for an input message.
- HMAC: Computes an HMAC authentication tag for an input message using an authentication key.
- HKDF-extract: Computes the HKDF-extract function that calculates a pseudorandom key from initial key material.
- HKDF-expand: Computes the HKDF-expand function that expands the pseudorandom key to several additional pseudorandom keys of desired lengths for specific cryptographic algorithms.
What’s Included?
- XIP3323B can be shipped in a number of formats, including netlist, source code, or encrypted source code.
- Additionally, synthesis scripts, a comprehensive testbench, and a detailed datasheet including an integration guide are included. .
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Security
Provider

Learn more about Hash / MAC IP core
Embedded Security explained: Cryptographic Hash Functions
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is HKDF/HMAC/SHA-384, SHA-384 IP Core with Extended Functionalities?
HKDF/HMAC/SHA-384, SHA-384 IP Core with Extended Functionalities is a Hash / MAC IP core from Xiphera Ltd listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.