Public Key Accelerator
Modern asymmetric cryptography algorithms such as RSA or elliptic curve cryptography over prime fields require complex mathematic…
Overview
Modern asymmetric cryptography algorithms such as RSA or elliptic curve cryptography over prime fields require complex mathematical calculations of large numbers up to 4096 bits. FortiPKA-RISC-V is a public key accelerator that allows offloading all the computationally heavy operations from the main CPU, while offering excellent balance between small footprint and high performance.
One of the key features of FortiPKA-RISC-V is a unique computation technology that eliminates the necessity for data transformations to and from the Montgomery domain, which leads to superior performance compared to alternative solutions. The efficient resource usage is ensured by implementation of cryptographic algorithms in firmware that is executed on an internal miniature RISC-V core. The core instruction set is extended to support custom modular arithmetic for large integers. Hardware configuration options are available to balance area and performance for specific applications. Moreover, FortiPKA-RISC-V supports CPU interfacing through AMBA AXI4, APB, AHB or custom memory-like slave interface.
To ensure smooth integration of FortiPKA-RISC-V to a customer’s product, a software library which performs high-level operations, such as encryption, decryption, signing and verifying for a variety of cryptographic algorithms is provided. Supported algorithms include RSA, DH, DSA, ECDH, ECDHE, ECDSA, EdDSA, DH and SM2. Additionally, FortiPKA-RISC-V's technology-agnostic design ensures compatibility across diverse semiconductor technologies.
FortiPKA-RISC-V includes all the necessary countermeasures against modern side-channel and fault injection attacks. The protection level is configurable, allowing to further improve security characteristics at the cost of resource usage or computation speed. To minimize the overhead of protections from physical attacks, countermeasures are employed in hardware, firmware and software when appropriate.
Key features
- Modular exponentiation operations with up to 4096-bit modulus
- Prime field ECC operations with up to 571-bit modulus
- Fastest implementation is 58 kGE and 68 Op/s for 2048-bit RSA, 431 Op/s for 1024-bit RSA, 150 Op/s for 384-bit scalar multiplication
- Smallest implementation is 33 kGE and 67 Op/s for 1024-bit RSA, 24 Op/s for 384-bit scalar multiplication
- Up to 350 MHz on the 45 nm process
- Unique mathematical solution that eliminates the need for preprocessing
- Software library with support for RSA, DH, DSA, ECDH, ECDHE, ECDSA, EdDSA, DH, SM2
- CPU interface support for AMBA AXI4, APB, AHB and custom memory-like slave interface
- RAM and ROM option for firmware storage
- Strong protection against modern side-channel and timing attacks, and fault injection attacks, tunable security level
- Technology agnostic
- Native support for standard NIST curves, optional support for custom curves
- Shared memories between host CPU and FortiPKA-RISC-V that enables memory reuse
- High level of customization on software, firmware and hardware level
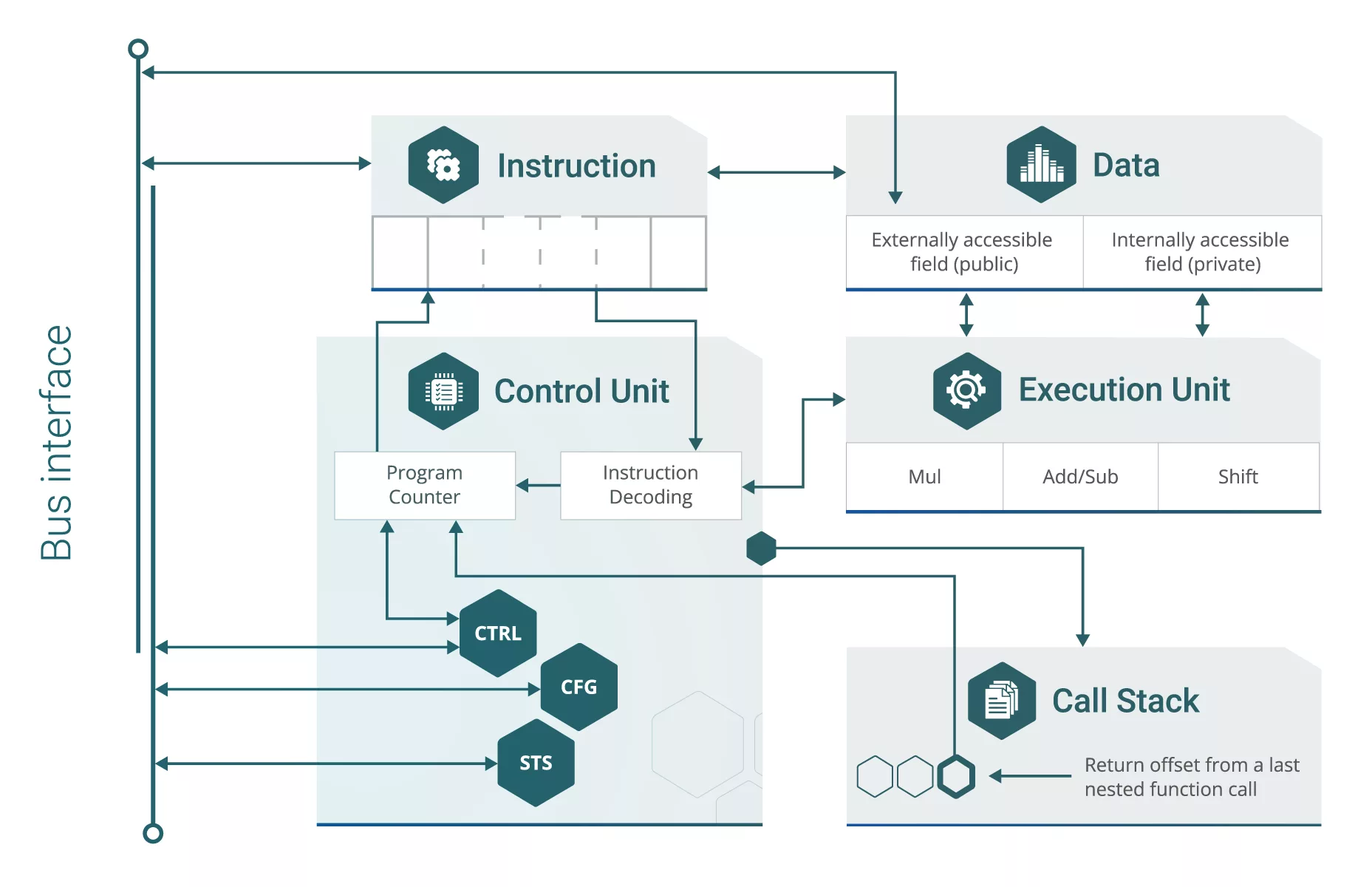
Block Diagram
Benefits
- Enhanced performance with no need for data preprocessing
- Optimal balance between high performance and low area
- Robust defense against side-channel and fault injection attacks, with customizable options to meet diverse cryptographic requirements
- Hardware configuration options allowing to optimize FortiPKA-RISC-V for specific applications
- Versatile CPU Interfaces: AMBA AXI4, APB, AHB, or a custom memory-like slave interface
- Extensive Algorithm Support: RSA, DH, DSA, ECDH, ECDHE, ECDSA, EdDSA, DH, and SM2
- Facilitation of memory reuse due to shared memory resources
- Seamless integration into customer products, supported by a comprehensive set of deliverables and documentation
Applications
- Networks
- Communications
- Payment Systems
- Authentication Devices
- IoT Devices
- Embedded Systems
What’s Included?
- SystemVerilog source code or netlist
- Testbench, input vectors and expected results
- Sample timing constraints, synthesis and simulation scripts
- Hardware Abstraction Layer (HAL) reference implementation
- Integration, configuration and usage manuals
- Firmware code
- Software library
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Public Key IP core
Securing the IoT: Part 1 - Public key cryptography
Smart Engine for Public Key cryptography
Public key cryptography and security certificates
Securing your apps with Public Key Cryptography & Digital Signature
Formally verifying AVX2 rejection sampling for ML-KEM
Frequently asked questions about Public-Key Cryptography IP cores
What is Public Key Accelerator?
Public Key Accelerator is a Public Key IP core from FortifyIQ, Inc. listed on Semi IP Hub.
How should engineers evaluate this Public Key?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Public Key IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.