ECC7 Elliptic Curve Processor for Prime NIST Curves
Elliptic Curve Cryptography (ECC) is a public-key cryptographic technology that uses the mathematics of so called “elliptic curve…
Overview
Elliptic Curve Cryptography (ECC) is a public-key cryptographic technology that uses the mathematics of so called “elliptic curves” and it is a part of the “Suite B” of cryptographic algorithms approved by the NSA.
The design is fully synchronous, with the exception of the seed part, and available in both source and netlist form.
The core is supplied as portable Verilog (VHDL version available) thus allowing customers to carry out an internal code review to ensure its security.
Function Description
The core implements either a point multiplication operation and the point verification operations, or (optionally) a complete digital signature operation (signing or signature verification). For the point multiplication version, the operands for the multiplication (k, Px, Py) are pushed into the core before the start of operation. Once the operation is completed, the result, Qx, Qy can be read from the core.
For the ECDSA version, for signing the input parameters (z, d, k) are pushed into the core and there (r,s) result can be read. For signature verification (z, Qx, Qy, r, s) are the input parameters. Here z is the hashed message, d is the private key, k is the nonce, r and s constitute the signature, Qx, Qy constitute the public key. A wrapper integrating multiple ECC7 cores with the hash cores and random number generators is available.
The curve and digital signature selections are fixed for the particular version of the core, for example the ECC7 P256-ECDSA-V core works with the NIST binary curve P-256 and implements the signature verification for the ECDSA algorithm.
The core implements either a point multiplication operation and the point verification operations, or (optionally) a complete digital signature operation (signing or signature verification). For the point multiplication version, the operands for the multiplication (k, Px, Py) are pushed into the core before the start of operation. Once the operation is completed, the result, Qx, Qy can be read from the core. For the ECDSA version, for signing the input parameters (z, d, k) are pushed into the core and there (r,s) result can be read. For signature verification (z, Qx, Qy, r, s) are the input parameters. Here z is the hashed message, d is the private key, k is the nonce, r and s constitute the signature, Qx, Qy constitute the public key. A wrapper integrating multiple ECC7 cores with the hash cores and random number generators is available. The curve and digital signature selections are fixed for the particular version of the core, for example the ECC7 P256-ECDSA-V core works with the NIST binary curve P-256 and implements the signature verification for the ECDSA algorithm.
Key features
- ECC7 implementation is unencumbered by any patents
- Support for NIST and NIST-like curves. For generic curves, see ECC8 family. Each core in the family is specialized for a single NIST curve (e.g., ECC7 P256 for P-256) or switchable between few curves.
- High throughput for long life battery powered applications: more than 1,000 point multiplications per second at 100 MHz clock
- Support for NIST prime curves P-192, P-224, P-256, P-384, or P-521
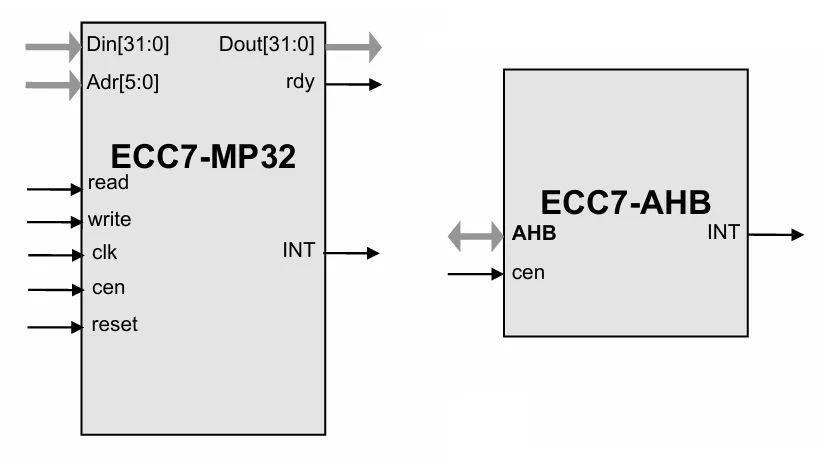
- Microprocessor-friendly interface. AHB wrapper available.
- Test bench provided
- Deliverables include Verilog test bench and test vectors
Block Diagram
Benefits
- Smallest core on the market, patent-free implementation
Applications
- Secure communications systems
- RFID
- Implantable medical devices
- Digital Rights Management (DRM) for battery powered electronics
- Elliptic Curve Diffie-Hellman (EC-DH) standard ANSI X9.63
- Blockchain processing
- Elliptic Curve Digital Signature Algorithm (EC-DSA) standard ANSI X9.62
- Digital Signature Standard (DSS) FIPS-186
- IEEE P1363
- TLS implementations per RFC 4492
- Cryptographic messaging per RFC 3278
- Windows Digital Right Management
- HDCP 2.x
What’s Included?
- Synthesizable Verilog RTL source code
- Test bench (self-checking)
- Test vectors
- Expected results
- Software Development Kit (SDK)
- User Documentation
Specifications
Identity
Security
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Public Key IP core
Securing the IoT: Part 1 - Public key cryptography
Smart Engine for Public Key cryptography
Public key cryptography and security certificates
Securing your apps with Public Key Cryptography & Digital Signature
Formally verifying AVX2 rejection sampling for ML-KEM
Frequently asked questions about Public-Key Cryptography IP cores
What is ECC7 Elliptic Curve Processor for Prime NIST Curves?
ECC7 Elliptic Curve Processor for Prime NIST Curves is a Public Key IP core from IP Cores, Inc. listed on Semi IP Hub.
How should engineers evaluate this Public Key?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Public Key IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.