Public Key Crypto Engine
The Public Key Crypto Engine is a versatile IP core for hardware offloading of all asymmetric cryptographic operations.
Overview
The Public Key Crypto Engine is a versatile IP core for hardware offloading of all asymmetric cryptographic operations. It enables any SoC, ASIC and FPGA to support efficient execution of RSA, ECC-based algorithms and more. The IP core is ready for all ASIC and FPGA technologies.
Complete asymmetric cryptography support
Elliptic Curve Cryptography (ECC) operations
- ECC operations up to 571 bits in F(p) and F(2m)
- ECDSA and ECDH support
- NIST, Brainpool, Koblitz curves, Montgomery, Edwards, Twisted-Edwards, SM2 and other curves
Modular Exponentiation operations
- RSA and RSA-CRT up to 8192 bits D
- SA and Diffie-Hellman (DH)
Other operations
- Curve25519/Curve448, EdDSA/Ed448, SRP and others Special operations: J-PAKE, ECMQV, ECIES, ECKCDSA
- Rabin-Miller (primality check)
Key features
- ASIC & FPGA
- RSA, ECC and more
- ECDH, ECDSA
- DSA, DH
- SM2, SM9
- 100% CPU offload
- DPA countermeasures
- Very small footprint & high performance
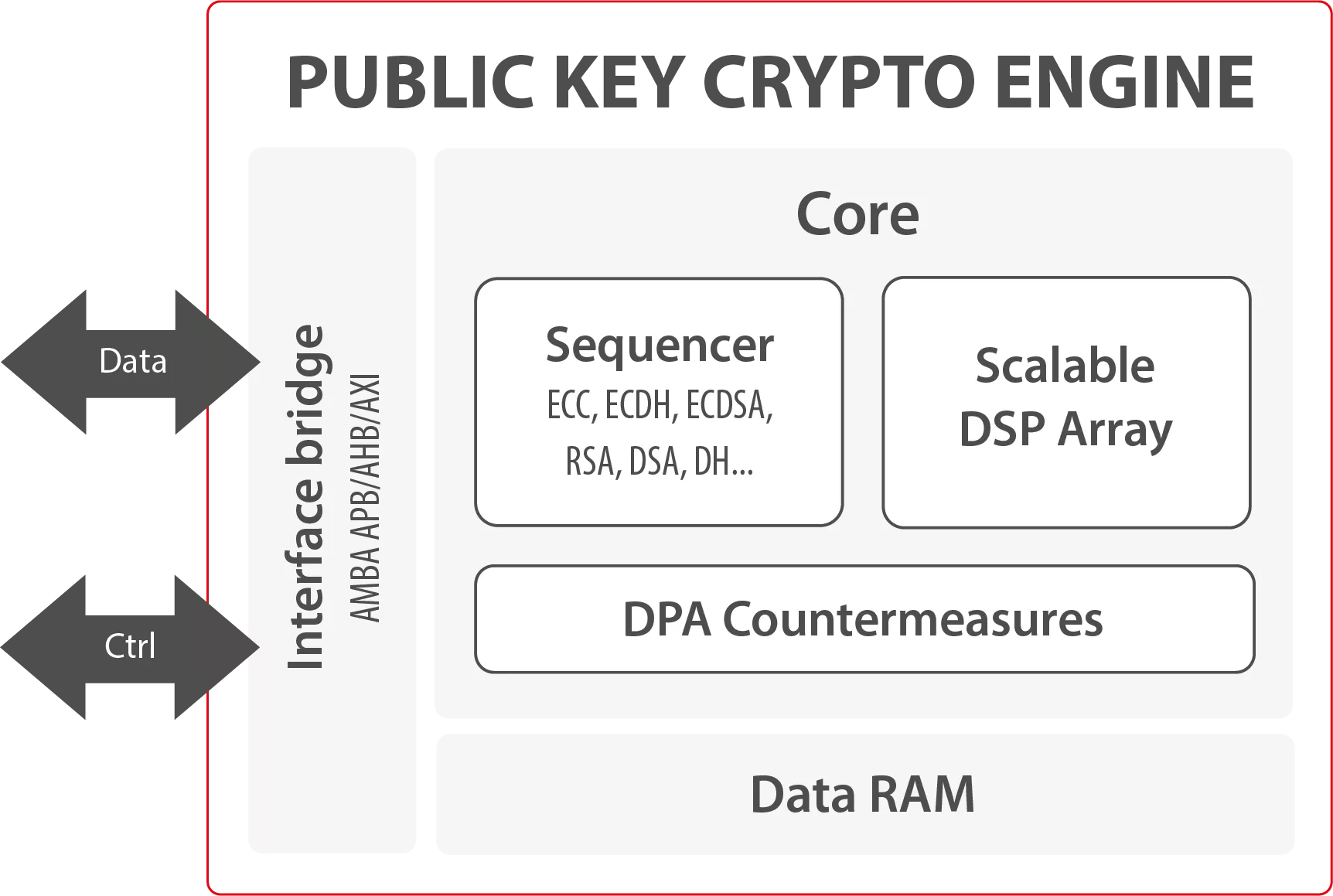
Block Diagram
Benefits
- Off-the-shelf
- 100% CPU off-load
- Unrivaled speed performance
- Optimal and tailored implementation to your needs
- Highest performance/area ratio for a large range of applications
- Reconfigurable and scalable features
- Portable and optimized to ASIC or FPGA technology
- Upgradeable to new performance requirements or to new generations of ASIC or FPGA technology
- User-friendly API
Applications
- MPU/MCU Crypto acceleration
- Hardware Security Module (HSM)
- Car-to-X
- Banking
- Government
- Enterprise VPN
- Industrial communications
- Networking security
- TLS/SSL
- IPsec
- Diffie-Hellman
What’s Included?
- Netlist or RTL
- Scripts for synthesis & STA
- Self-checking TestBench based on FIPS vectors
- Documentation
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Public Key IP core
Securing the IoT: Part 1 - Public key cryptography
Smart Engine for Public Key cryptography
Public key cryptography and security certificates
Securing your apps with Public Key Cryptography & Digital Signature
Formally verifying AVX2 rejection sampling for ML-KEM
Frequently asked questions about Public-Key Cryptography IP cores
What is Public Key Crypto Engine?
Public Key Crypto Engine is a Public Key IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Public Key?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Public Key IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.