KYBER IP Core
Kyber IP is a core designed for Kyber post-quantum Key Encapsulation Mechanism (KEM).
Overview
Kyber IP is a core designed for Kyber post-quantum Key Encapsulation Mechanism (KEM). It currently supports the Encapsulation and Decapsulation functions, with key generation functionality planned for future implementation. This IP is fully compliant with the Kyber specification submitted during Round 3 of the NIST Post-Quantum Cryptography Standardization process. Additionally, Kyber IP will be enhanced in the future to achieve compliance with ML-KEM (FIPS-203).
Key features
- supports encapsulation and decapsulation operations
- supports all modes K=2,3,4.
- is compliant with Kyber specification round 3.
- has fully stallable input and output interfaces.
- Key generation feature is going to be implemented in the near future.
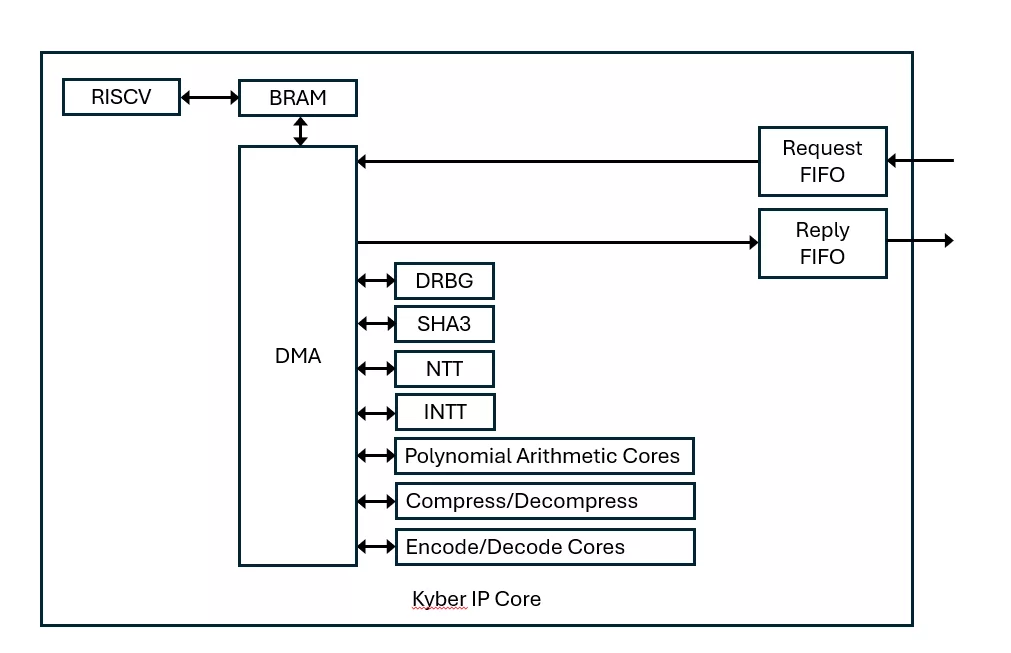
Block Diagram
What’s Included?
- Encrypted Netlist
- Synthesis Scripts
- Comprehensive Documentation
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Security
Provider

- Design IP Cores
- Design & Verification Services: ASIC / FPGA and Embedded Systems’ development
- Functional Safety Consultancy & Training Services
- Trainings: Wide range of trainings with more than 150 different trainings
Learn more about Post Quantum IP core
How to design secure SoCs Part IV: Runtime Integrity Protection
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Why Anti-tamper Sensors Matter: Agile Analog and Rambus Deliver Comprehensive Security Solution
Frequently asked questions about Post-Quantum Cryptography IP cores
What is KYBER IP Core?
KYBER IP Core is a Post Quantum IP core from ElectraIC listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.