Learn more about Symmetric Crypto IP core
The cybersecurity threat landscape is dynamic and rapidly evolving. Indeed, attackers are constantly finding new ways to exploit critical vulnerabilities across a wide range of applications and devices. Protecting data and devices requires secure processes running on systems and networks.
The goal of this white paper is to provide a primer introduction to RoT and how to choose a right RoT as the trust anchor for a novel hardware based security architecture
A Root of Trust is the foundation on which all secure operations of a computing system depend. It contains the keys used for cryptographic functions and enables a system-wide secure boot process. It is inherently trusted and therefore must be secure by design.
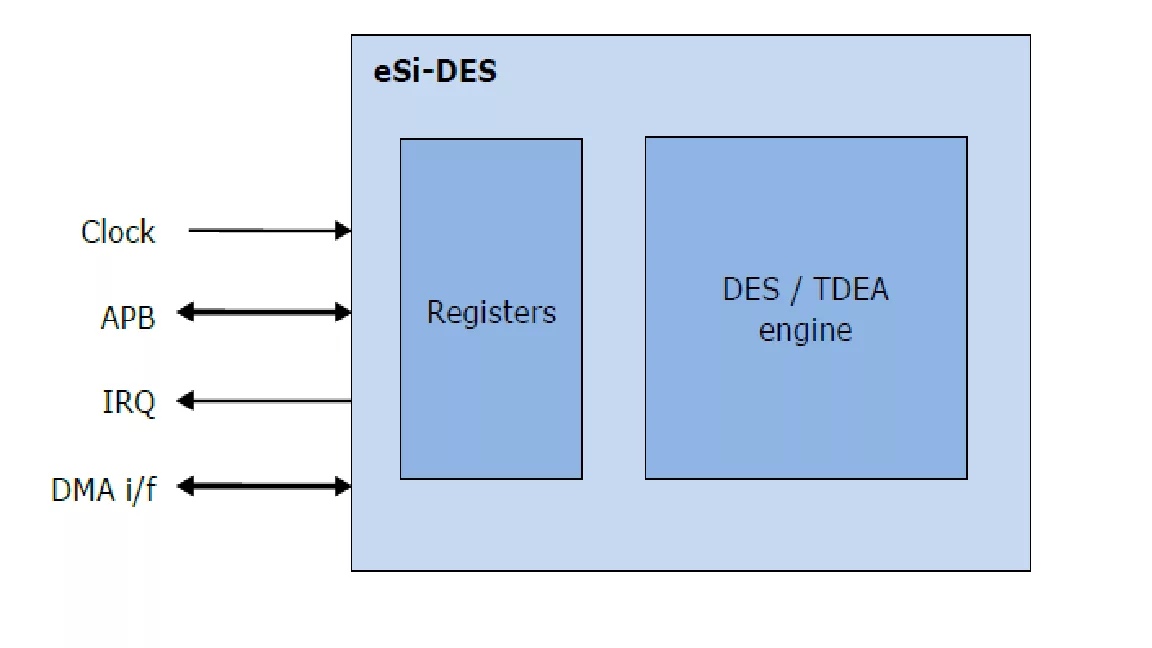
Encryption requirements are now found in almost every new SoC design. This paper focuses on symmetric offload in a packet processing system for IPsec but the concepts apply equally well to SSL, SRTP and link security.