Integrated Security Services Platform (iSSP)
Secure-IC offers the first worldwide PQC ready Security Lifecycle Management solution.
Overview
Secure-IC offers the first worldwide PQC ready Security Lifecycle Management solution.
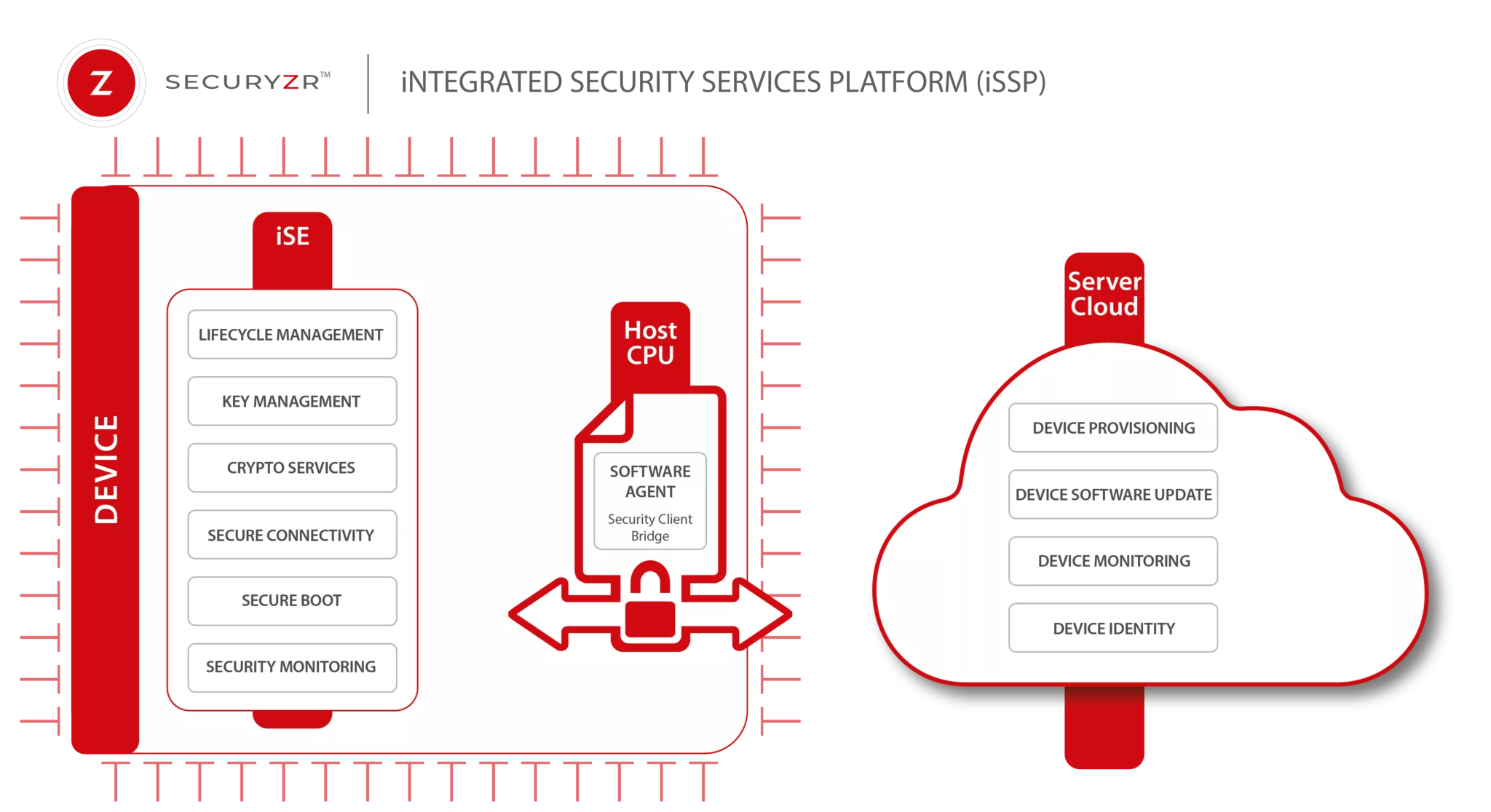
The Securyzr™ iSSP (integrated Security Services Platform) enables Secure-IC customers and partners to supply, deploy and manage the embedded security of their devices’ fleet all along their lifecycle. The Securyzr™ iSSP is an easy & trustful end-to-end solution for zero-touch security lifecycle services such as provisioning, firmware update, security monitoring & device identity management.
The preferred version of the platform combines 3 key elements :
- Securyzr™r iSE (integrated Secure Element) as the Root-of-Trust to protect the overall system from chip level with the higher security coverage.
- Securyzr™Host SW Framework as a package of robust APIs (Application Programming Interfaces) & connectivity layers to ensure protected communication between the iSE, the host chip & the server.
- Securyzr™Server as a package of remote security services & protected communication channels.
The solution is completed by a software agent to provide connectivity from Chip-to-Cloud (and vice-versa).
The security of the systems will be easily visualized through a Security Digital Twin.
In addition to these three solutions, Secure-IC provides secure connectivity solutions which are composed of two parts:
- Secure connectivity protocols which offer implementation of security protocols such as MACSec, IPSec
- Software security which consists of software implementations of cryptographic algorithms. These implementations can be protected against several kinds of attacks.
Block Diagram
Video
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Root Of Trust IP core
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Rambus RT-660 Root of Trust IP Achieves FIPS 140-3 Certification
Extending Security IP leadership with FIPS 140-2 CMVP Certification for Root of Trust IP
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Root of Trust IP cores
What is Integrated Security Services Platform (iSSP)?
Integrated Security Services Platform (iSSP) is a Root Of Trust IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.