Hardware Security Module
Hardware security module IP core with function to support crypto key storage, boot authentication, supervision, and offloading of…
Overview
Hardware security module IP core with function to support crypto key storage, boot authentication, supervision, and offloading of cryptographic functions.
GRHSM is an isolated system-on-chip (SoC) that can be used as a subsystem in a larger SoC design to implement a hardware security module or otherwise provide security functions to the larger system. Use cases include crypto key storage, boot authentication,supervision, and offloading of cryptographic functions.
GRHSM depends on platform-specific capabilities to implement its features, utilizing non-volatile on-chip memory in ASSPs and unique bitstreams in FPGAs
Key features
- Root of Trust
- Provides a hardware-based Root of Trust with a unique, immutable device ID
- Supports cryptographic verification of device identity and integrity
- Generate Public Key Infrastructure (PKI) keypairs that it can use to sign messages, including random number based challenges
- Authentication and secure communication
- Ability to perform authentication, integrity verification and assets encryption/decryption using symmetric or asymmetric keys (PKI). Supports also Post-Quantum Cryptography (PQC) algorithms for future-proof security
- Supports session establishment and encrypted data exchange via standard protocols, including PQC algorithms
- Key Management
- Secure generation, derivation and operation of symmetric and asymmetric keys
- Key secure storage and erasure
- Predefined or static keys may be stored in on-chip memory or in an external flash only accessible by GRHSM
- Generated keys are stored in an external flash memory only accessible by GRHSM
- Secure Random Number Generation
- Based on NIST SP 800-90A/B structure
- Hardware accelerated cryptographic functions (NIST FIPS 180-4, 197, 198-1, 202)
- SHA-256, SHA-3, AES 128, AES 256, HMAC, HKDF
- Self-Protection and Isolation
- Hardware-based isolation ensures separation from external SoC and system resources
- Minimal external communication, based on mailbox interface, limits attack vectors
- Operations
- Users can customize the platform and manage secret keys using their proprietary software libraries
- The software running on the Hardware Security Module determines how to manage keys, facilitates secure key operations, boot authentication, and communication setup
- Debug
- The Hardware Security Module has a dedicated interface for debugging and customization
- The debug interface can be permanently disabled after deployment
- Debug and customization activities are facilitated via the GRMON debug tool.
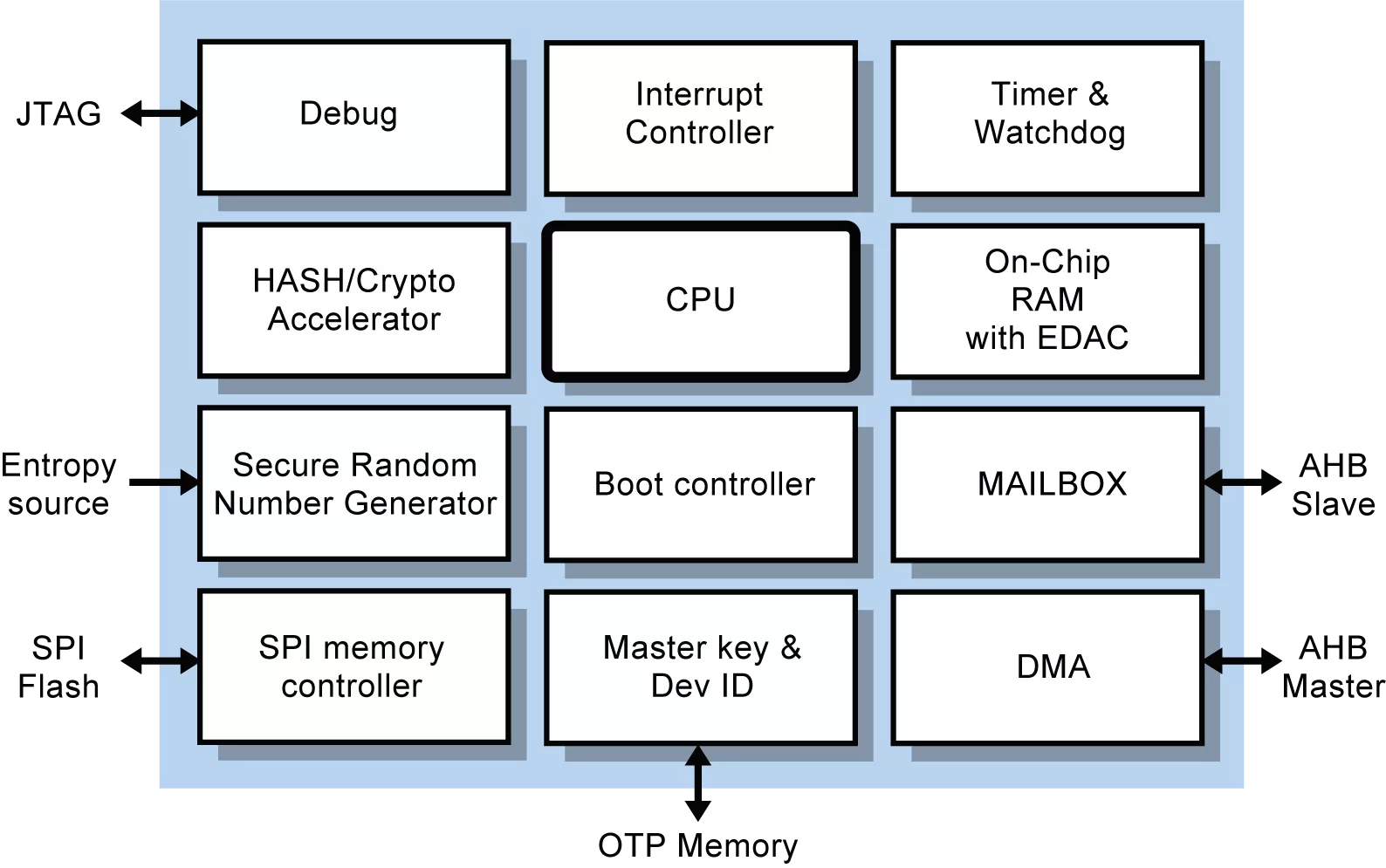
Block Diagram
Specifications
Identity
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Root Of Trust IP core
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Rambus RT-660 Root of Trust IP Achieves FIPS 140-3 Certification
Extending Security IP leadership with FIPS 140-2 CMVP Certification for Root of Trust IP
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Root of Trust IP cores
What is Hardware Security Module?
Hardware Security Module is a Root Of Trust IP core from Frontgrade Gaisler listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.