Root of Trust solutions
Securyzr™ integrated Secure Element (iSE) is Secure-IC Root of Trust solution.
Overview
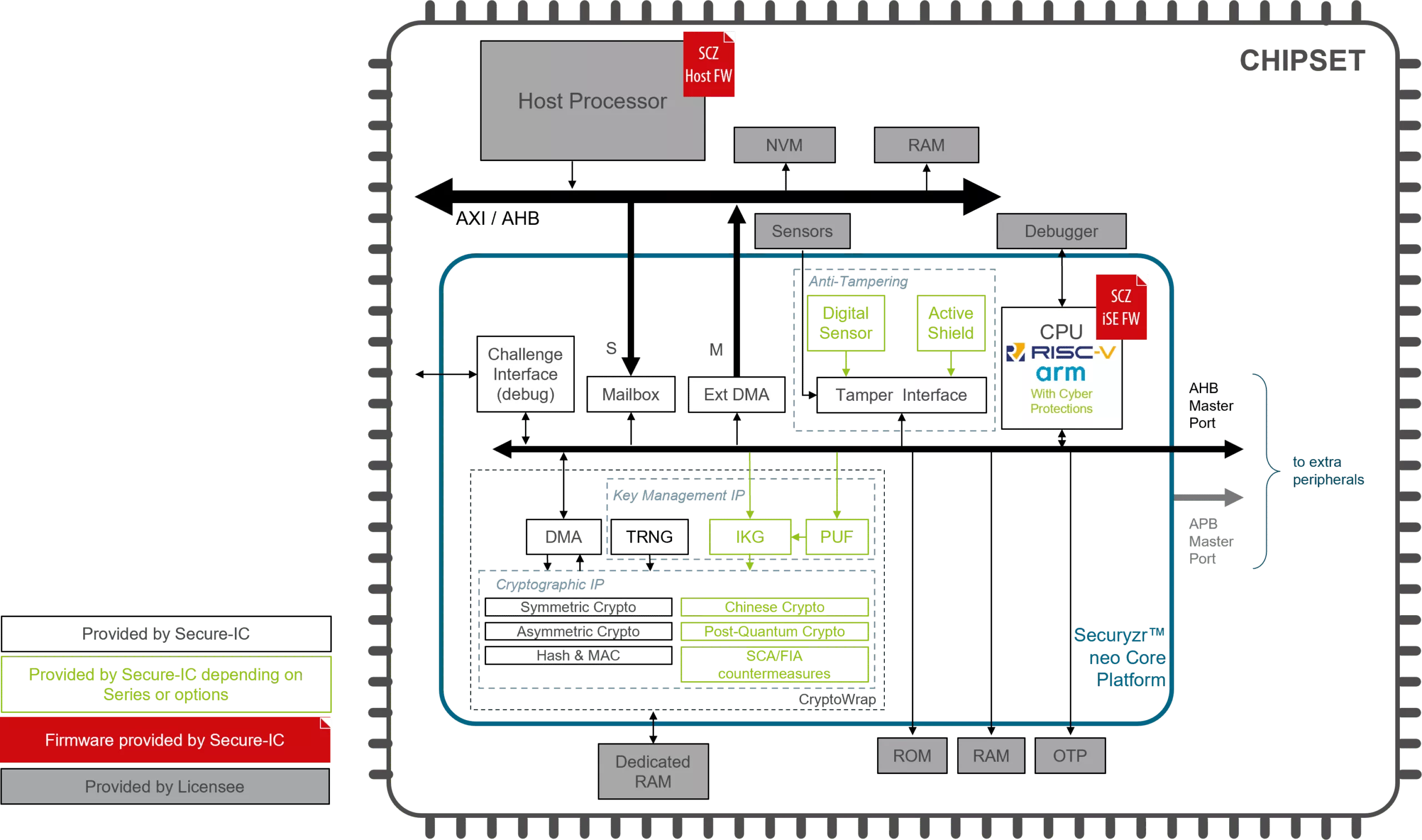
Securyzr™ integrated Secure Element (iSE) is Secure-IC Root of Trust solution. Embedded in the main SoC, it offers multiple services to its host system: provisioning, secure boot, secure firmware update, cryptographic services, multiple protections, etc.
Thanks to its dual computation and strong isolation, it offers an additional layer of security compared to trusted execution environment. The module is highly flexible and fits all applications of the heterogeneous Internet-of-Things ecosystem, from the ultra-low power sensor to the connected car.
Key features
HARDWARE
- Tunable Crypto: Authentication and confidentiality of the incoming/outcoming data. PQC is supported.
- Key Management: Management of cryptographic keys in a system.
- Physical Attack Protection: Protection against side-channel attacks and fault injection attacks.
- Anti-Tampering: Protection against fault injection attacks with Active Shield and Digital Sensor
- Cyber Escort Unit: Solution which increases the security by checking the integrity of executed code on any CPUs.
SOFTWARE
- Secure Provisioning: Using secure communication protocols for the initial setup and configuration of a device or system.
- Secure Boot: Verify the physical and logical integrity of the platform, and guarantee the authenticity of the software and OS running on the device.
- Secure Update: New features updates/removal can quickly be implemented
- Secure Monitoring: Ensure that no physical or cyber-attack is being perpetrated on the system and apply the security policy in case of attack.
- Secure Debug: For first programming, debug purpose, key injection/generation, lifecycle management, on-site firmware injection/update, malfunctioning device update authorization in factory.
Block Diagram
Benefits
- Easy to integrate
- Tunable solution
- Fully digital
- AMBA interface
- Strong technical support (HW and SW)
Applications
- The SecuryzrTM iSE is a very efficient solution to enable any secure application on chip. The hardware module shielded from the main processor brings a high level of security. Also the hardware offloading of the cryptographic operations from the main processor to the SecuryzrTM iSE module guarantees a low power operation. The SecuryzrTM iSE module is tuned to the target application in terms of feature and performance.
What’s Included?
- Technical specifications document including User manual, Integration guideline, Test Plan
- VHDL RTL code
- VHDL testbench and scripts for simulation
- RTL of the AMBA wrapper
- Securyzr FW (source code)
- Securyzr Firmware for Host CPU
- Support for integration
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Root Of Trust IP core
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Rambus RT-660 Root of Trust IP Achieves FIPS 140-3 Certification
Extending Security IP leadership with FIPS 140-2 CMVP Certification for Root of Trust IP
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Root of Trust IP cores
What is Root of Trust solutions?
Root of Trust solutions is a Root Of Trust IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.