Secure Debug Hardware IP
The Secure Debug IP provides isolation between 2 domains.
Overview
The Secure Debug IP provides isolation between 2 domains. It will ensure isolation between the HOST System on one hand, and the HSM System on another hand. Both(HOST an dHSM)can access the IP through an AXI Slave interface.
Secure-IC’s Secure Debug IP is a hardware IP that provides:
- Hardware Authentication scheme between the HOST and the HSM.
- Communication interface between the HOST and the HSM,mainly for the purpose of the maintenance of the System-on-Chip.
This IP is controlled by a HOST through an AXI Slave Interface. The purpose of the Secure Debug IP is to provide the following services:
- Get life-cycle information from the HSM.
- Provide a Hardware Authentication scheme.
- Allow only one HOST to be logged in at the same time.
- Allow to open the HSM debug por tonly if life cycle mode values allow it.
- Receive Maintenance requests (first programming, update, lifecycle ...) from an external user.
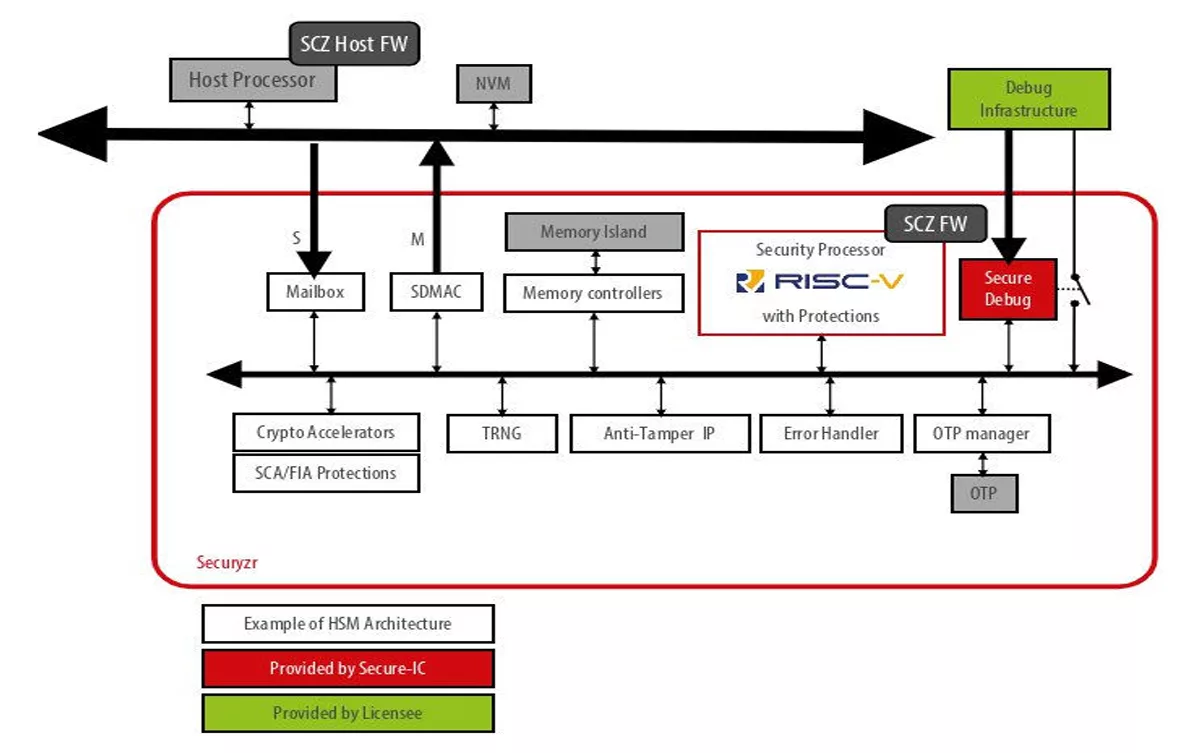
Block Diagram
Applications
- Automotive
- IoT
- eHealth
- Defense
- Payments
- Servers
- Smart Grid
- Identity
- Media & Entertainment
- Memory & Storage
- Consumer Electronics
- Edge & Cloud
- Trusted Computing
- AI
- Printer
- Industry
What’s Included?
- RTL code
- SW Drivers
- Scripts for implementation
- Self-checking RTL test-bench
- Documentation
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Root Of Trust IP core
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Rambus RT-660 Root of Trust IP Achieves FIPS 140-3 Certification
Extending Security IP leadership with FIPS 140-2 CMVP Certification for Root of Trust IP
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Root of Trust IP cores
What is Secure Debug Hardware IP?
Secure Debug Hardware IP is a Root Of Trust IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.