Cyber Escort Unit IP: Bridging Software and Hardware Security Gaps
The Cyber Escort Unit is designed to fill the security gap between software cyber security and hardware by escorting step by step…
Overview
The Cyber Escort Unit is designed to fill the security gap between software cyber security and hardware by escorting step by step the program execution to achieve high execution performances in a secure way, allowing advantageously real-time detection of zero-day attacks. Unique on the market, this product builds the foundation for hardware-enabled cybersecurity.
It is the only tool on the market that comprises technologies for detecting and deterring cyberattacks. This technology acts on-the-fly. Precisely, Secure-Call is aiming to protect against the four threats which represent a large number of vulnerabilities encountered in practice.
- Return oriented programming (ROP): The attacker reuses chunks of code to assemble a malicious program like a patchwork.
- Stack Smashing, by exploiting a buffer over run or integer under-or-overflow etc.: the attacker crafts some fake stack frames in order to change the program context.
Properties
- Detect all return address corruption on the stack
- No impact on computation time
- Very easyset-up
- No recompilation needed, no influence on the protected program
- Can be used in a safety context, i.e., restore PC, so that the system comes back to a stable state
Key features
- Real-time detection of Zero-Day attack by monitoring step by step the program execution
- Stops the attack before it is executed
- Compared to SW level cyber protection, it cannot be exploited remotely, as it is inaccessible to an attacker
- Ensures protection against Fault Injection Attack (Temperature, Electromagnetic Injection,Clock Glitch, Power Glitch, Laser Injection) and Software Cyber Attack (Code Injection, Buffer Overflow, Stack Smashing, Control Flow Graph hijacking, 0-day attacks targeting SW execution)
- Allows to limit false positive alarms as it is checking fundamental properties of well-behaved code
- No processor modification
- Runtime impact highly limited (<1% in most cases)
- Low hardware footprint
- Agnostic for the program
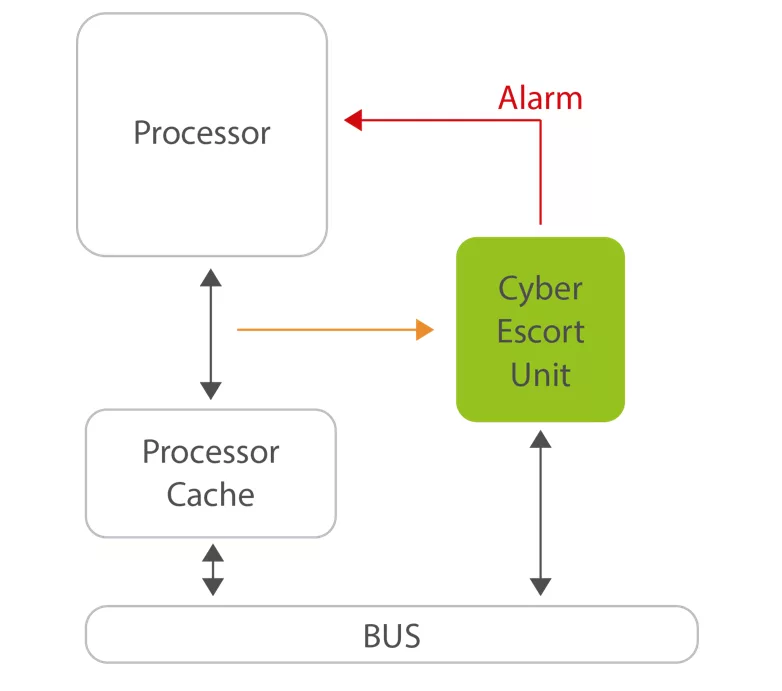
Block Diagram
Applications
- Secure Boot
- Zero-day attacks
- Cyber andphysical attacks targeting the code execution
What’s Included?
- Obfuscated VHDL RTL of the IP
- Self-checking RTL Testbench based on reference scenario for simulation
- User manual, integration guideline and test plan
Specifications
Identity
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Root Of Trust IP core
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Rambus CryptoManager Root of Trust Solutions Tailor Security Capabilities to Specific Customer Needs with New Three-Tier Architecture
Rambus RT-660 Root of Trust IP Achieves FIPS 140-3 Certification
Extending Security IP leadership with FIPS 140-2 CMVP Certification for Root of Trust IP
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Root of Trust IP cores
What is Cyber Escort Unit IP: Bridging Software and Hardware Security Gaps?
Cyber Escort Unit IP: Bridging Software and Hardware Security Gaps is a Root Of Trust IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Root Of Trust?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Root Of Trust IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.