SHA-256 Secure Hash Function
The SHA256 IP core from Alma Technologies is a high performance implementation of the SHA-256 Message Digest algorithm, a one-way…
Overview
The SHA256 IP core from Alma Technologies is a high performance implementation of the SHA-256 Message Digest algorithm, a one-way hash function, compliant with FIPS 180-2.
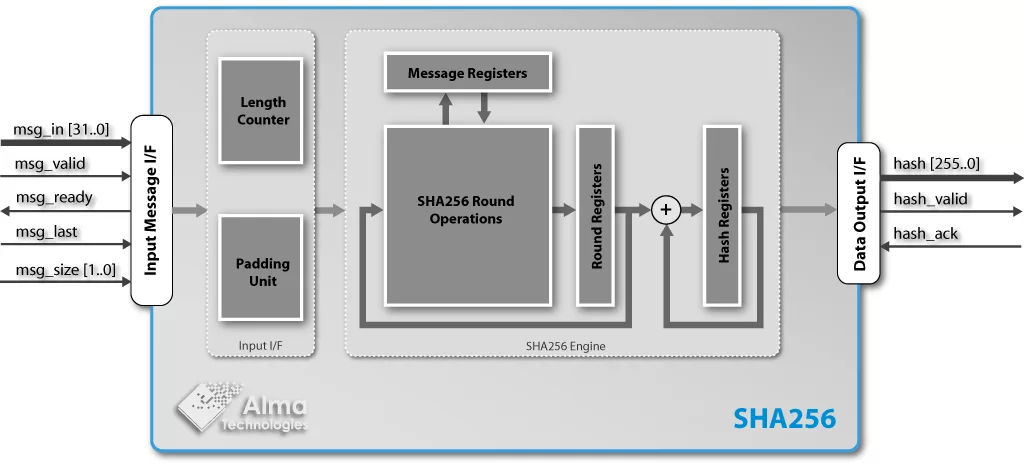
The core is composed of two main units, the SHA256 Engine and the Padding Unit as shown in the block diagram. The SHA256 Engine applies the SHA256 loops on a single 512-bit message block, while the Padding Unit splits the input message into 512-bit blocks and performs the message padding on the last block of the message.
The processing of one 512-bit block is performed in 66 clock cycles and the bit-rate achieved is 7.75Mbps / MHz on the input of the SHA256 core.
The SHA256 core is equipped with easy to use fully stallable interfaces both for input and output. These are designed to permit the user's application to stop the data stream from the core when it is not able to receive data or to stop the input stream towards the core according to data arrival rate.
Key features
- Compliant to FIPS 180-2 specification of SHA-256.
- Bit padding internally implemented.
- Supports 2^64-1 bits maximum message length.
- Supports input message length multiple of 8-bit.
- Initial value of the chaining variables selected before synthesis.
- 66 processing cycles per 512-bit message block.
- User Programmable Initial Vector.
- Fully stallable input and output interfaces, ideal for streaming applications.
- Designed for Easy Integration
- Optimum design for ASIC or FPGA implementations.
- Comprehensive documentation and a complete verification environment, including a bit-accurate model.
Block Diagram
What’s Included?
- Clear-text RTL sources for ASIC designs, or pre-synthesized and verified Netlist for FPGA and SoC devices
- Release Notes, Design Specification and Integration Manual documents
- Bit Accurate Model (BAM) and test vector generation binaries, including sample scripts
- Pre-compiled RTL simulation model and gate-level simulation netlist for the FPGA Netlist license
- Self-checking testbench environment sources, including sample BAM generated test cases
- Simulation and sample Synthesis (for ASICs) or Place & Route (for FPGAs) scripts
Specifications
Identity
Security
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Hash / MAC IP core
Embedded Security explained: Cryptographic Hash Functions
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is SHA-256 Secure Hash Function?
SHA-256 Secure Hash Function is a Hash / MAC IP core from Alma Technologies listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.