Overview
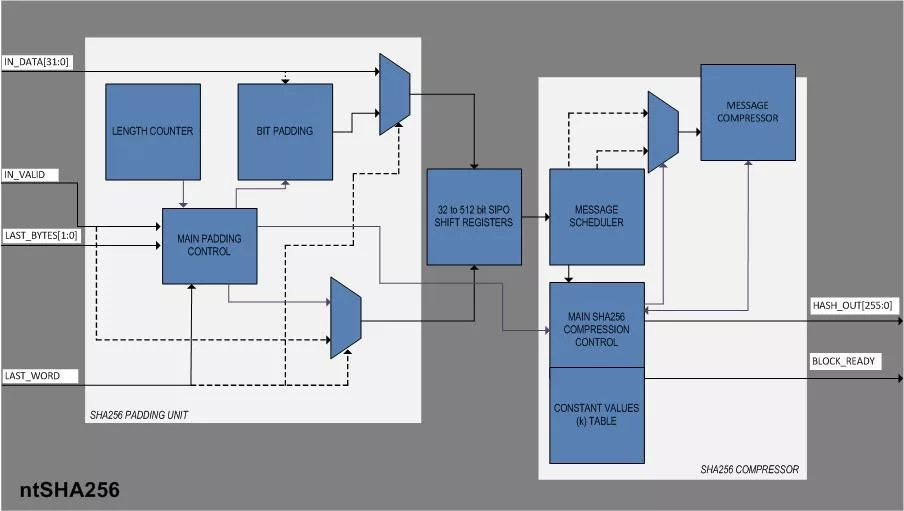
An n-bit hash is a map from arbitrary length messages to n-bit hash values. An n-bit cryptographic hash is an n-bit hash which is one-way and collision resistant. Such functions are important cryptographic primitives used for such things as digital signatures and password protection. Current popular hashes produce hash values of length n = 128 (MD4 and MD5) and n = 160 (SHA-1), and therefore can provide no more than 64 or 80 bits of security, respectively, against collision attacks. Since the goal of the new Advanced Encryption Standard (AES) is to offer, at its three cryptovariable sizes, 128, 192, and 256 bits of security, there is a need for companion hash algorithms which provide similar levels of enhanced security. ntSHA256 IP Core implements SHA-256, or Secure Hash Algorithm-256 which is one of the latest hash functions standardized by the U.S. Federal Government. It is a 256-bit hash and is meant to provide 128 bits of security against collision attacks. The implementation is very low on latency, high speed with a simple interface for easy integration in SoC applications.
Learn more about Hash / MAC IP core
A complete reinvention of the automotive industry is currently underway. Autonomous driving, connected vehicles, and the electrification of the powertrain all represent a once-in-a-generation shift in the manufacturing process.
Explore the significance of cryptographic hash functions in embedded security, their common algorithms, and practical choices for FPGA-based systems.
TLS 1.3 offers attractive speed and security improvement benefits that are hard to ignore. The handshake phase was sped up by removing one or more roundtrips (back and forth messaging between client and server) in TLS 1.3 – with “or more” meaning that for certain cases, roundtrips can be entirely eliminated (0-RTT).
In this column, after a background introduction, we will first discuss IEEE 802.1AR standard on secure device identity. Next, we’ll assert PUF is an enabling solution for the device eID. Third, we will discuss PUF related international standards. Fourth, we will present a short tutorial on PUFiot. Fifth, we will assert that PUFiot is an ideal Device eID with wide applications. Finally, we will draw a conclusion on the future trend of Device eID development.
Data centers require many low-level network services to implement high-level applications. Key-Value Store (KVS) is a critical service that associates values with keys and allows machines to share these associations over a network. Most existing KVS systems run in software and scale out by running parallel processes on multiple microprocessor cores to increase throughput.
With the advent of IoT and increasingly interconnected and autonomous nature of a vehicle’s control modules, there has been an exponential increase in V2V, V2X and inter vehicular communications. This in turn increases the attack surface for hackers which demands state-of-art security features in modern automotive microcontrollers, moreover safety and security go hand in hand.