HASH Core, providing MD5, SHA1 and SHA256. Includes DMA and AXI Interface
This is a high performance, small footprint HASH IP Core.
Overview
This is a high performance, small footprint HASH IP Core. It supports three HASH algorithms: MD5, SHA1, SHA256. A S/G DMA engine keeps the core running. Each hash engine has it’s own dedicated clock, which is independent of the main AXI clock.
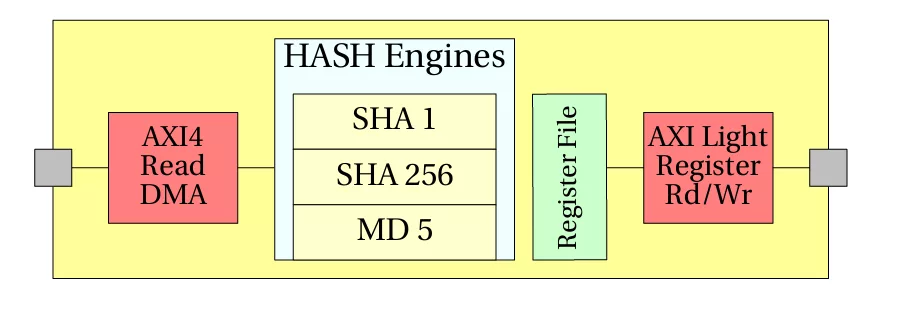
ARCHITECTURE
The HASH IP Core performs 3 different HASH calculation. Witch HASH is to b e used is determined in the CSR register. Once a starting TD address has been set, the DMA engine can be enabled. It will process TDs until it encounters a TD with the NEXT field of zero.
Key features
- Supports MD5, SHA1 and SHA256
- High Performance S/G DMA engine
- Fully AXI-4 compatible
- AXI-Light for register Interface
- Separate clocks for MD5, SHA and SHA256 engines and AXI interface
Block Diagram
Benefits
- High Performance, small footprint
What’s Included?
- Verilog Source Code
- Test bench
- Tech Support
Specifications
Identity
Security
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Hash / MAC IP core
Embedded Security explained: Cryptographic Hash Functions
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is HASH Core, providing MD5, SHA1 and SHA256. Includes DMA and AXI Interface?
HASH Core, providing MD5, SHA1 and SHA256. Includes DMA and AXI Interface is a Hash / MAC IP core from ASICS World Services, LTD. listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.