Hash Crypto Engine
The Hash Crypto Engine is flexible and optimized hash IP core compliant with FIPS 180-3 (HASH functions), FIPS 198 (HMAC function…
Overview
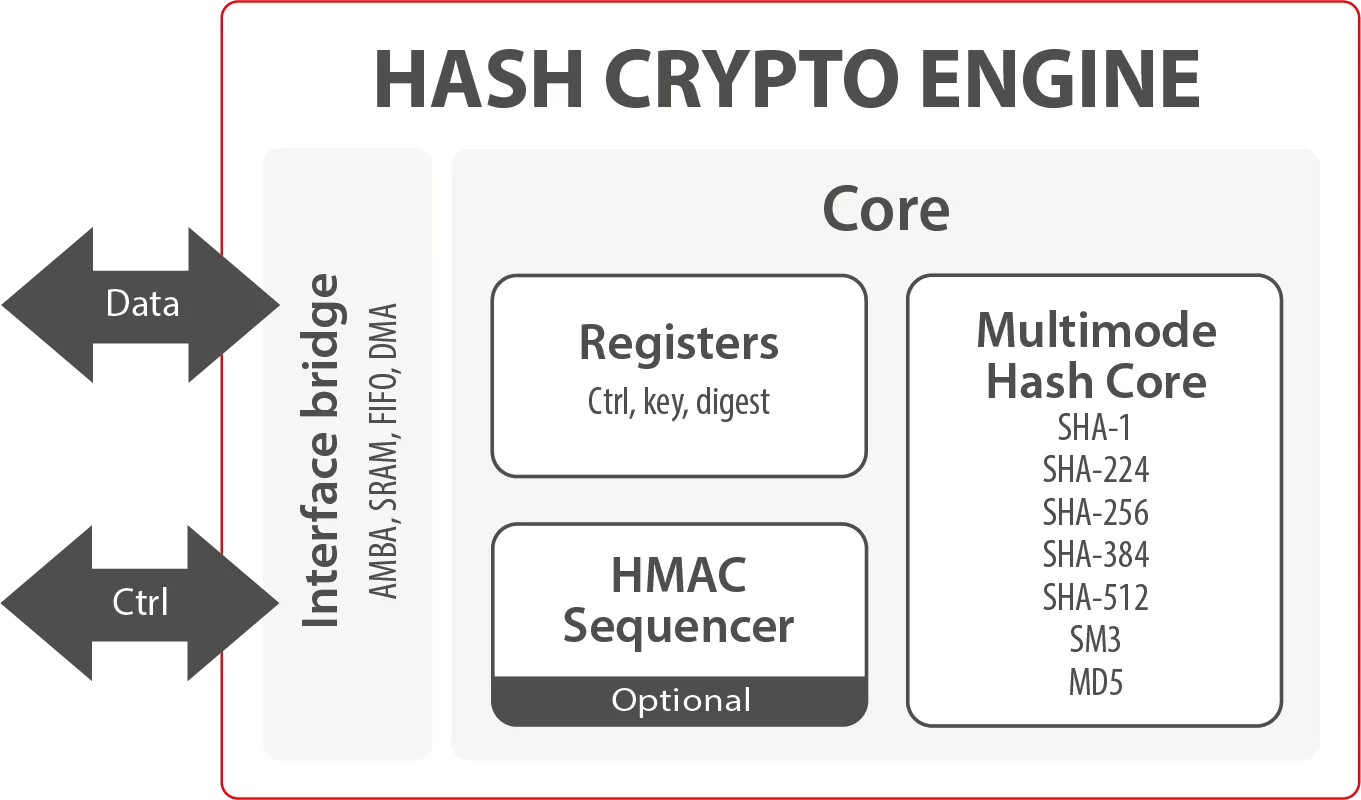
The Hash Crypto Engine is flexible and optimized hash IP core compliant with FIPS 180-3 (HASH functions), FIPS 198 (HMAC function) and OSCCA (SM3).
With a flexible wrapper supporting a wide selection of programmable hashing modes (SHA-1, SHA-224, SHA-256, SHA-384, SHA-512, SM3 and MD5) with HMAC and several options of data interface, the Hash Crypto Engine is an easy-to-use solution with predictable resources and performances on ASIC and FPGA.
Implementation aspects
The Hash Crypto Engine is easily portable to ASIC and FPGA. It supports a wide range of applications on various technologies. The unique architecture enables a high level of flexibility. The throughput and features required by a specific application can be taken into account in order to select the most optimal and compact configuration.
Key features
- ASIC and FPGA
- Supports:
- SHA-1
- SHA-224
- SHA-384
- SHA-512
- SM3
- MD5
- Supports HMAC
- Message padding in software or hardware
- Low power feature
- Data interface: AMBA (AHB/AXI) with optional DMA
- AMBA (APB, AXi-4 Lite) Configuration Interface
- Control interface: APB/AXI4-lite
Block Diagram
Benefits
- Off-the-shelf, predictable and silicon-proven solution
- Logic footprint optimized to used hash functions
- Supports several hash functions
- Easy to integrate
- User-friendly Software API
- Portable and optimized to ASIC or FPGA technology
Applications
- Digital signature
- Key derivation
What’s Included?
- Netlist or RTL
- Scripts for synthesis
- Self-checking Testbench based on FIPS vectors
- Datasheet
- Integration guide
Specifications
Identity
Files
Note: some files may require an NDA depending on provider policy.
Provider
Learn more about Hash / MAC IP core
Embedded Security explained: Cryptographic Hash Functions
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is Hash Crypto Engine?
Hash Crypto Engine is a Hash / MAC IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.