SHA3 IP Core
SHA3 IP Cores perform cryptographic hashing in compliance with the SHA-3 (Secure Hash Algorithm 3) specifications defined in 'FIP…
Overview
SHA3 IP Cores perform cryptographic hashing in compliance with the SHA-3 (Secure Hash Algorithm 3) specifications defined in 'FIPS 202'. This standard specifies methods for generating secure hash values using the SHA-3 algorithm.
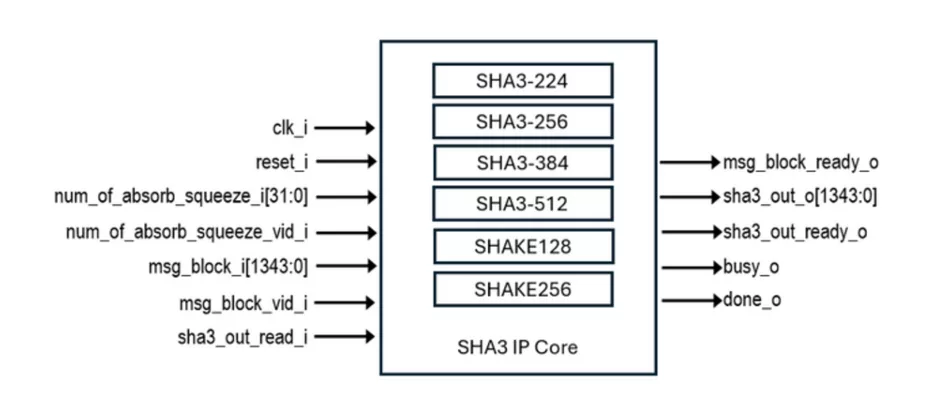
SHA3 IP Cores support the SHA3-224, SHA3-256, SHA3-384, SHA3-512, SHAKE128, and SHAKE256 functions, and are byte-oriented in their implementation. VHDL is used as the Hardware Description Language of the IP Core. AXI4-Stream interface can be designed and provided upon request.
Key features
- supports hashing for functions listed below:
- SHA3-224
- SHA3-256
- SHA3-384
- SHA3-512
- SHAKE128
- SHAKE256
- is compliant with FIPS 202.
- has fully stallable input and output interfaces.
Block Diagram
What’s Included?
- Encrypted Netlist
- Synthesis Scripts
- Comprehensive Documentation
- SHA3 Validation SystemTestbenches in SystemVerilog
Specifications
Identity
Security
Files
Note: some files may require an NDA depending on provider policy.
Provider

- Design IP Cores
- Design & Verification Services: ASIC / FPGA and Embedded Systems’ development
- Functional Safety Consultancy & Training Services
- Trainings: Wide range of trainings with more than 150 different trainings
Learn more about Hash / MAC IP core
Embedded Security explained: Cryptographic Hash Functions
Embracing a More Secure Era with TLS 1.3
Standardized PUF-based Solution for Device eID
Implementing Ultra Low Latency Data Center Services with Programmable Logic
Security in vehicular systems
Frequently asked questions about Hash / MAC IP cores
What is SHA3 IP Core?
SHA3 IP Core is a Hash / MAC IP core from ElectraIC listed on Semi IP Hub.
How should engineers evaluate this Hash / MAC?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Hash / MAC IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.