IPSEC AES-256-GCM (Standalone IPsec)
XIP7213E implements the Internet Protocol Security (IPsec) as standardised in RFC4303 and RFC4305.
Overview
XIP7213E implements the Internet Protocol Security (IPsec) as standardised in RFC4303 and RFC4305. The IPsec protocol defines a security infrastrucure for Layer 3 (as per the OSI model) traffic by assuring that a received packet has been sent by the transmitting station that claimed to send it. Furthermore, the traffic between stations is both encrypted to provide data confidentiality and authenticated to provide data integrity.
XIP7213E uses Advanced Encryption Standard [1] (AES) with 128/256-bit key in Galois Counter Mode (GCM) [2] to protect data confidentiality, data integrity and data origin authentication. The cipher suite is denoted as GCM-AES(-XPN)-128/192/256 and with 8/12/16 byte authentication tag. Both 32 or 64-bit sequence numbering is supported. XIP7213E uses Xiphera’s extreme-speed AESGCM IP core XIP1113E as the underlying building block for Authenticated Encryption and Associated Data (AEAD).
Secure Association Database (SAD) lookup for frames is performed by XIP7213E independently and Secure Association (SA) management (IKEv2 / RFC4306) is offloaded to a CPU/MCU via separate secure interface.
XIP7213E has been designed for easy integration with FPGA- and ASIC-based designs in a vendoragnostic design methodology, and the functionality does not rely on any vendor or process-specific features
Functionality
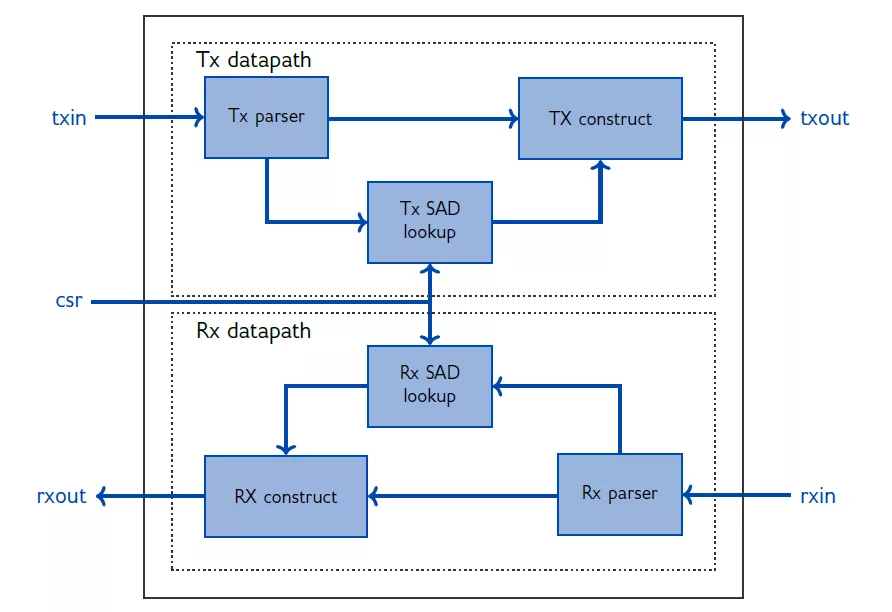
The functionality of XIP7213E is divided into the transmit (Tx) and receive (Rx) datapaths, which operate independently of each other. The underlying cipher suite AES-GCM is consequently instantiated for both the Rx and Tx datapaths.
IPsec operation is based on the concepts of unidirectional Security Associations (SA) within each channel. Each SA uses its own Secure Association Key (SAK); establishing and managing keys is not part of the IPsec standard.
The high-level functionality of Tx datapath includes parameter lookup based on source and destination IPs, ports and protocol. Based on these parameters the IP constructs the TX output frame with encrypted and authenticated ESP frame. TX path also has an option to insert IKEv2 frames from internal buffer, which can be updated by CPU interface.
The high-level functionality of RX datapath includes IPsec frame detection, either based on ESP protocol type or UDP encapsulated frames, with port numbers 500 or 4500. IKEv2 frames are regonised based on SPI information and state of IKEv2 process.
XIP7213E also supports the bypass mode, where an incoming packet passes through the XIP7213E unaltered.
Key features
- Performance: The extreme-speed XIP7213E achieves a throughput exceeding 100 Gbps range in modern high-end FPGAs and ASIC process nodes. Notably XIP7213E does not require any extra idle cycles, even when it processes short packets.
- Standard Compliance: XIP7213E is compliant with the IPsec protocol as standardised in RFC4303 [4] / RFC4306[3]. The cipher suite (GCM-AES-128/192/256) is fully compliant with the Advanced Encryption Algorithm (AES) standard [1], as well as with the Galois Counter Mode (GCM) standard [2].
- Fully standalone IPsec engine, requiring no external CPU or software intervention for packet encryption, authentication, or flow management, offers performance, security, low power consumption and ease of validation.
- Flexible key management interface with IKEv2 support, enabling smooth integration with existing security frameworks and automated key lifecycle handling.
- CAVP validated: The underlying cryptographic algorithm implementations in the XIP7213E have received [5] Cryptographic Algorithm Validation Program (CAVP) [6] validation. 1
Block Diagram
Applications
- Data Center, Cloud, and Edge Security
- Virtual Private Networks (VPNs)
- FPGA-based SmartNICs
Specifications
Identity
Security
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Symmetric Crypto IP core
CXL - The Latest Specification in Secured Network Traffic
Securing your apps with Public Key Cryptography & Digital Signature
RoT: The Foundation of Security
Tailoring Root Of Trust Security Capabilities To Specific Customer Needs
Symmetric Cryptographic Offload Options for SoC Designers
Frequently asked questions about Symmetric Cryptography IP cores
What is IPSEC AES-256-GCM (Standalone IPsec)?
IPSEC AES-256-GCM (Standalone IPsec) is a Symmetric Crypto IP core from Xiphera Ltd listed on Semi IP Hub.
How should engineers evaluate this Symmetric Crypto?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Symmetric Crypto IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.