Digital Fault Injection Attack Detector
In cryptography, an attack can be performed by injecting one or several faults into a device thus disrupting the functional behav…
Overview
In cryptography, an attack can be performed by injecting one or several faults into a device thus disrupting the functional behavior of the device. Techniques commonly used to inject faults consist in introducing variations in the source voltage, clock frequency, temperature, or irradiating with a laser beam etc.
Unlike analog sensors which are dedicated to the detection of a specific perturbation attack, the Digital Sensor is designed to detect various threats belonging to the family of Fault Injection Attacks (FIA):
- Input clock frequency (clock glitches, overclocking)
- Input voltage (power glitches, underfeeding)
- Temperature (heating)
- Radiations (laser spot, light spot, electromagnetic)
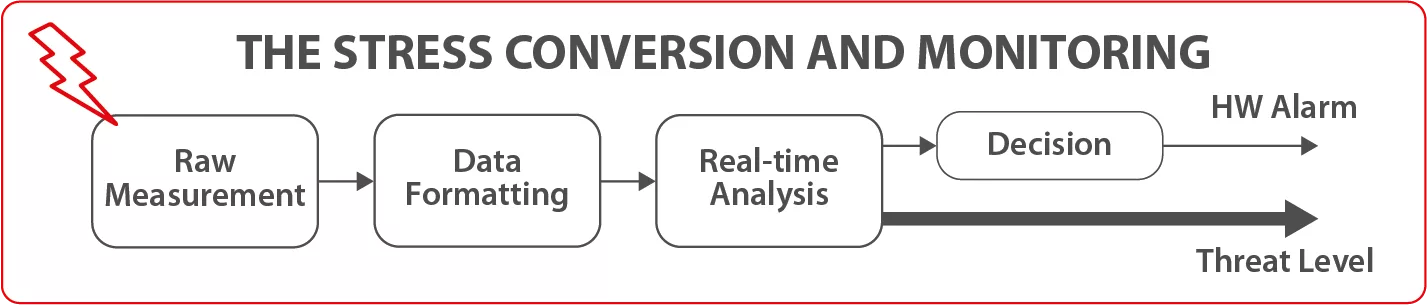
Digital Sensor converts all monitored stresses into a timing stress which is then measured. When a threat is detected, it provides the system with a measurement of the threat’s level and it raises the hardware alarm.
Key features
- Detects global and local fault injections such as laser, EMFI, clock or temperature
- Difficult to identify by an attacker (melted within the rest of design)
- Real-time hardware alarm
- Embeds health-test to validate the integrity of the IP during the boot and on-demand
- Proven technology with stochastic model for reliability and security estimation
- Tested in the Security Science Factory Lab, using global stress (e.g., clock glitch) and local stress (e.g., electromagnetic injection)
- Security certification ready (incl. Common Criteria)
- Fully digital and designed with the standard cells library
- Transferable to any design kit
- Lightweight
- Customizable sensitivity
- Compatible with clock gating feature
- Several sensors can be regrouped around a unique bus interface
- No calibration after design
- Support DVFS
- Easy to integrate into the system
- AMBA (APB, AHB, AXI) interface
Block Diagram
Applications
- IoT
- Set-top Box
- Mobile
- Automotive
- Defense
- Etc.
What’s Included?
- Technical specifications
- Front-end RTL and constraints files .sdc
- Integration guidance for back-end
- Self-checking RTL Testbench based on reference scenario for simulation
- Remote support for integration
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Fault Injection Protection IP core
What Does a GPU Have to Do With Automotive Security?
Introducing agileSecure anti-tamper security portfolio
Unlocking the Power of Digital Twins in ASICs with Adaptable eFPGA Hardware
How to design secure SoCs, Part II: Key Management
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Fault Injection Protection IP cores
What is Digital Fault Injection Attack Detector?
Digital Fault Injection Attack Detector is a Fault Injection Protection IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Fault Injection Protection?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Fault Injection Protection IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.