Active Shield
Attacks on digital circuits can occur when an attacker attempts to physically alter the device's internal components.
Overview
Attacks on digital circuits can occur when an attacker attempts to physically alter the device's internal components. These types of attacks are known as intrusive and can include actions such as probing or manipulating signals, adding or removing components, or modifying features on the chip.
To counteract these threats, Secure-IC has developed the Active Shield technology. This technology uses a protective mesh layer over the sensitive parts of the circuit, and actively monitors the mesh integrity for any signs of tampering. This countermeasure helps to safeguard the circuit's features and components, such as metal routing and transistors, from unauthorized access or modification through the front side of the device, such as:
- Wire micro-probing to read or force an equipotential
- Wire cutting (e.g., alarms, entropy source disconnection from a true random number generator…)
- Wire re-routing
- Burnt fuses opening
- ROM Altering
Active monitoring
In order to further deter intrusive attacks, the mesh is actively monitored using random cryptographically generated patterns to detect integrity violations. By using this technology, modifying and rerouting the mesh becomes very costly as the attacker must reroute many wires to avoid detection. In addition, the data travelling through the shield mesh cannot be predicted by the attacker, because it is output by a cryptographic block cipher.
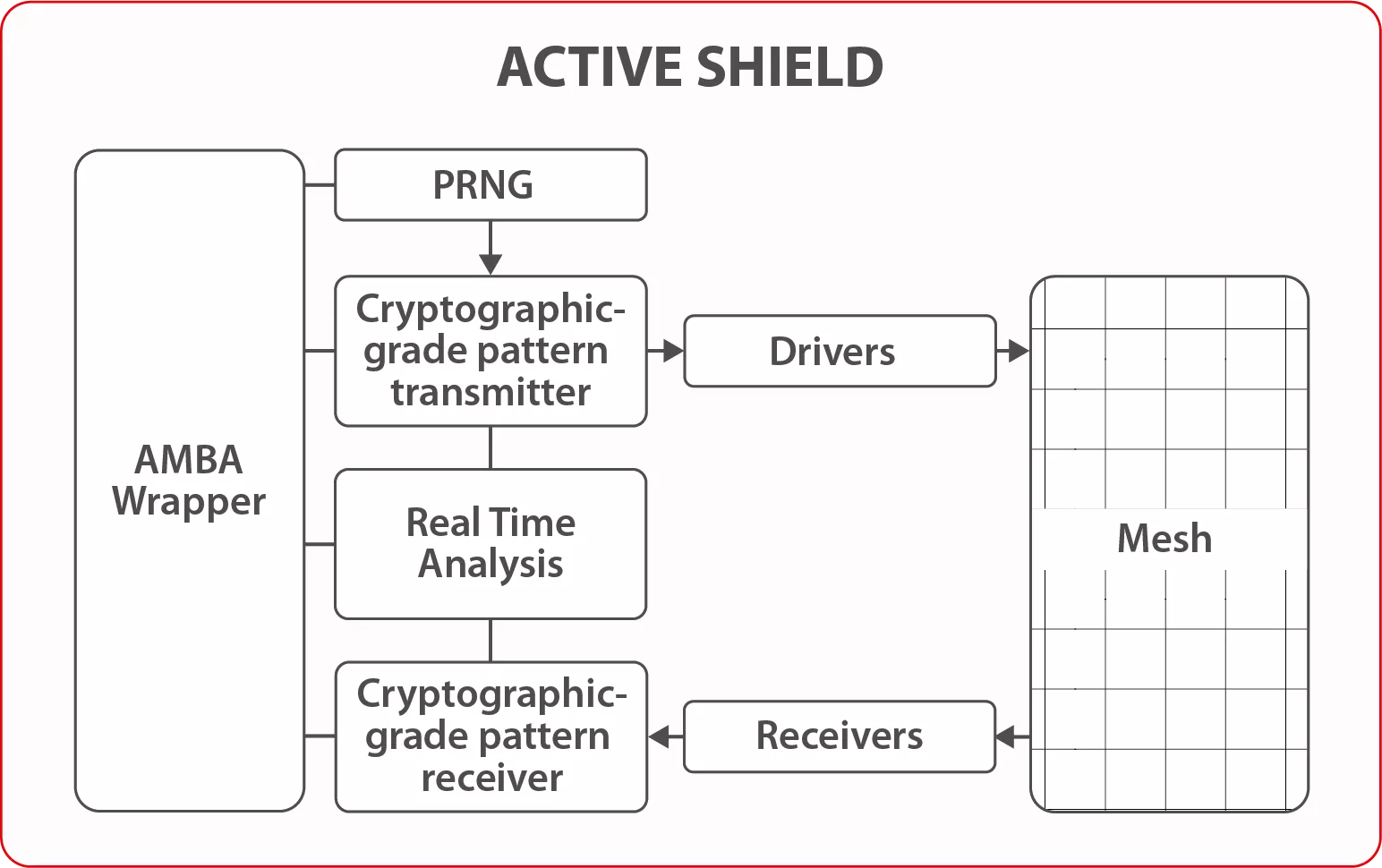
Active Shield technology relies on several submodules:
- A mesh created using a metal layer for wire routing
- Drivers and receivers used for electrical connection with the mesh
- A cryptographic-grade tamper detection module for monitoring the mesh integrity
Ideal for
Active Shield IP is ideal for:
- Protection against Bus probing
- Protection against FIB attacks
- Protection against wire micro-probing to read or force an equipotential
- Protection against wire cutting (e.g., alarms, entropy source disconnection from a true random number generator)
- Protection against wire re-routing
- Protection against ROM altering
Key features
- Anti-tamper solution with a mesh placed over the sensitive parts of the circuit and actively monitored
- Uses random cryptographically generated patterns to detect integrity violations
- Antenna-effect safe
- Security certification ready (incl. Common Criteria)
- Fully digital and designed with the standard cells library
- Mesh designed with scripts
- Mesh can be interleaved with P/G network in topmost layers (no need to sacrifice a layer)
- Compatible with clock gating to reduce the power consumption
- Transferable to any design kit
- Lightweight
- No calibration after design
- Easy to integrate into the system
- AMBA (APB, AHB, AXI) interface
Block Diagram
Applications
- IoT
- Setup Box
- Mobile
- Automotive
- Defense
What’s Included?
- Technical specifications document including User manual, Integration guideline, Test Plan
- VHDL RTL code for the shield
- VHDL testbench and scripts for simulation
- RTL of the AMBA wrapper
- Constraints file (.sdc)
- Innovus scripts to place and route the shield
- Support for integration
Files
Note: some files may require an NDA depending on provider policy.
Specifications
Identity
Provider

Learn more about Fault Injection Protection IP core
What Does a GPU Have to Do With Automotive Security?
Introducing agileSecure anti-tamper security portfolio
Unlocking the Power of Digital Twins in ASICs with Adaptable eFPGA Hardware
How to design secure SoCs, Part II: Key Management
Why Hardware Root of Trust Needs Anti-Tampering Design
Frequently asked questions about Fault Injection Protection IP cores
What is Active Shield?
Active Shield is a Fault Injection Protection IP core from Secure-IC listed on Semi IP Hub.
How should engineers evaluate this Fault Injection Protection?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Fault Injection Protection IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.