Overview
The DSHA2-384 - a universal solution that accelerates SHA2-384 hash with HMAC mode.
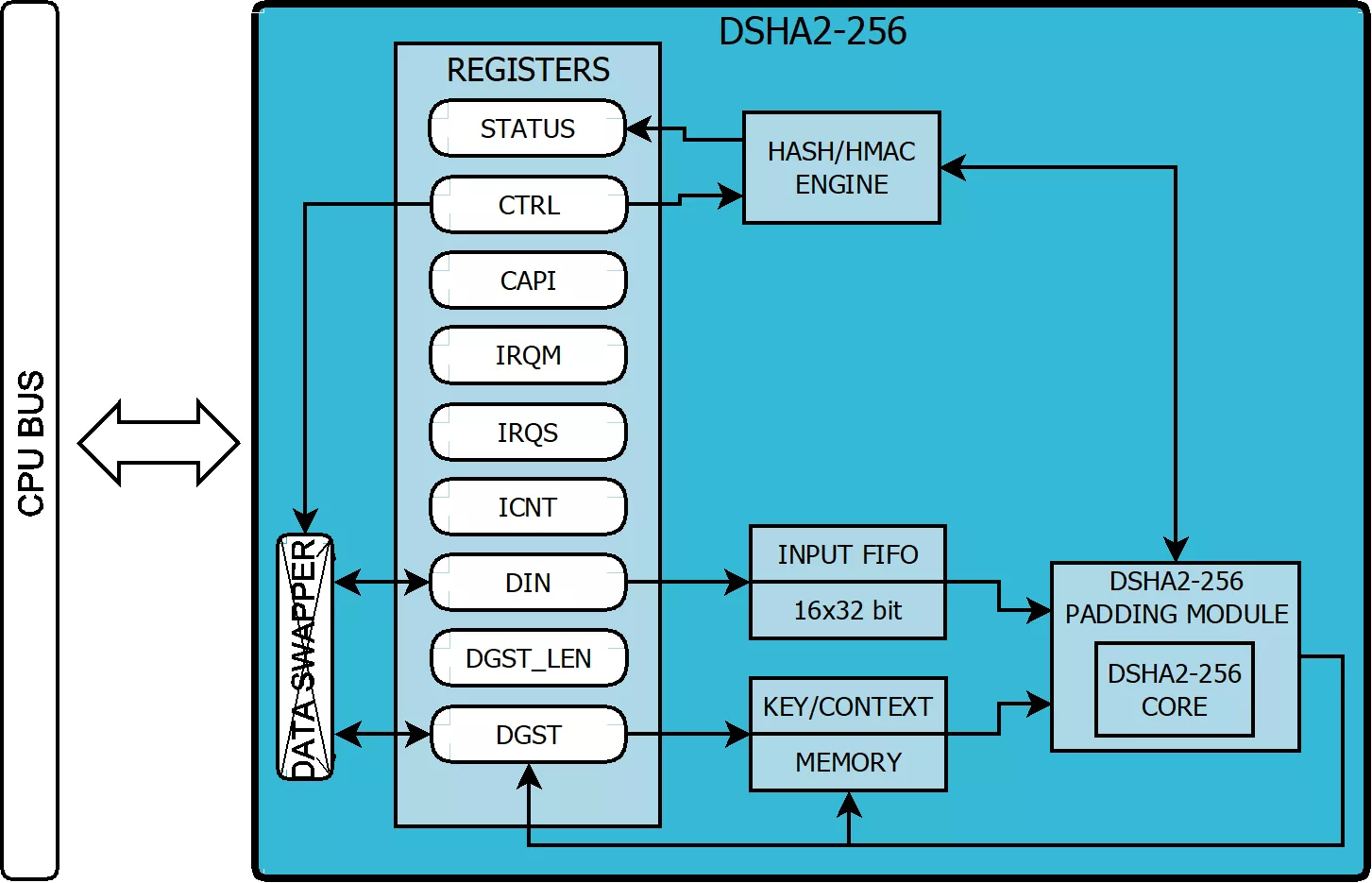
DSHA2-384 bridge to APB, AHB, AXI bus, it is a universal solution that efficiently accelerates SHA2-384 hash function compliant with FIPS PUB 180-4. It computes message digest in either 256, 224, or 384-bit modes. Allowed input message length is up to 264 – 1 bit. Depending on the core configuration it also natively supports the SHA2-384 HMAC (Keyed-Hash Message Authentication Code), a cryptographic function defined in RFC 2104. This IP is suitable for authenticity and data integrity verification in digital signature protocols and generally in secure communication. It might also be used in accelerating cryptocurrency computations. What is more, it offers a context-swapping feature, which might be used in complex systems with a task’s preemption mechanism. Its other application can be software managed or a custom HMAC scheme. SHA2 is a family of cryptography that secures one-way compression functions based on the Merkle-Damgard structure, the 256 version sequentially processes 512-bit input blocks during 64 rounds. From arbitrary length input message (maximum 264 – 1 bits) it produces fixed 256 or 224-bit length digest in a way, that it is practically infeasible to invert it (get an original message from its digest). Such a property is called a one-way function. The cryptographic security of SHA2-384 is assumed at 128-bit level (112-bit in the case of SHA2-224) which makes it appropriate for use in security applications. Some of these applications need to prove knowledge or possession of some secret data while computing message digest. For such authentication purposes, the HMAC function has been designed. It combines both secret key and cryptography secure hash function (like SHA2-256).
Learn more about Hash / MAC IP core
A complete reinvention of the automotive industry is currently underway. Autonomous driving, connected vehicles, and the electrification of the powertrain all represent a once-in-a-generation shift in the manufacturing process.
Explore the significance of cryptographic hash functions in embedded security, their common algorithms, and practical choices for FPGA-based systems.
TLS 1.3 offers attractive speed and security improvement benefits that are hard to ignore. The handshake phase was sped up by removing one or more roundtrips (back and forth messaging between client and server) in TLS 1.3 – with “or more” meaning that for certain cases, roundtrips can be entirely eliminated (0-RTT).
In this column, after a background introduction, we will first discuss IEEE 802.1AR standard on secure device identity. Next, we’ll assert PUF is an enabling solution for the device eID. Third, we will discuss PUF related international standards. Fourth, we will present a short tutorial on PUFiot. Fifth, we will assert that PUFiot is an ideal Device eID with wide applications. Finally, we will draw a conclusion on the future trend of Device eID development.
Data centers require many low-level network services to implement high-level applications. Key-Value Store (KVS) is a critical service that associates values with keys and allows machines to share these associations over a network. Most existing KVS systems run in software and scale out by running parallel processes on multiple microprocessor cores to increase throughput.
With the advent of IoT and increasingly interconnected and autonomous nature of a vehicle’s control modules, there has been an exponential increase in V2V, V2X and inter vehicular communications. This in turn increases the attack surface for hackers which demands state-of-art security features in modern automotive microcontrollers, moreover safety and security go hand in hand.