Post-Quantum Key Encapsulation IP Core
The KiviPQC-KEM is an IP core implementing the ML-KEM (Module-Lattice-based Key Encapsulation Mechanism) a post-quantum cryptogra…
Overview
The KiviPQC-KEM is an IP core implementing the ML-KEM (Module-Lattice-based Key Encapsulation Mechanism) a post-quantum cryptographic standard defined by NIST FIPS 203. Engineered to withstand both classical and quantum computer attacks, ML-KEM enables two parties to securely establish a shared secret key.
Supporting all ML-KEM parameter sets, the KiviPQC-KEM enables:
- Two parties to securely establish a shared secret key over an untrusted public channel
The IP core provides dedicated hardware acceleration for the most computationally demanding operations, ensuring high throughput and low latency while keeping the logic footprint compact.
Designed as a standalone, self-contained module, the KiviPQC-KEM can be integrated seamlessly into any SoC design. It features a standard AMBA® AXI4-Lite interface for straightforward hardware integration and platform-independent C code, HAL, and API drivers for simple software integration into host processor.
Key features
- NIST FIPS 203 compliant
- Supports ML-KEM 512/768/1024 parameter sets
- Supports ML-KEM.KeyGen, ML-KEM.Encaps/Decaps functions
- Self-contained engine with a minimal attack surface
- Hardware offloading and acceleration for ML-KEM operations
- Protection against timing-based side channel attacks
Easy integration
- Platform agnostic design for any FPGA
- AMBA® AXI4-Lite Interface
- Platform agnostic C-Source Code
- HAL, API and Software drivers included
- Software examples included
- Software User Guide included
- Fast support response within 8 hours
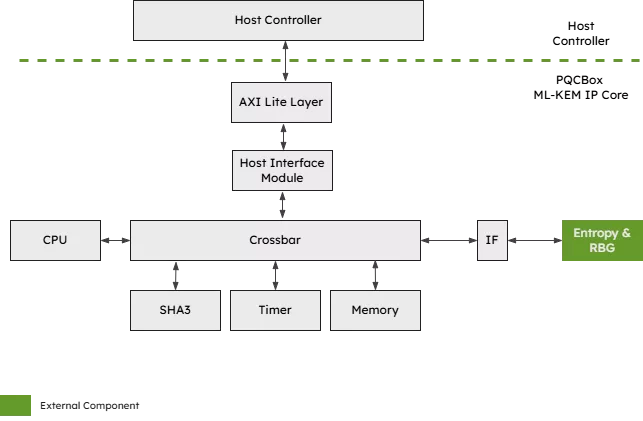
Block Diagram
Benefits
- Easy integration Saves time and effort: Ready to use hardware and software integration.
- Highly cost-efficient: Saves costs: Post-Quantum IP Core with low licensing costs and free evaluation licences.
- Minimal logic utilization: Saves resources: Designed and optimized for area-constrained devices.
Applications
- Quantum-Resistant Networks
- Public Key Infrastructures
- Network Security: MACsec, IPsec
- Transport Protocols: TLS, SSL
- Secure Communications
- Electronic Transactions
What’s Included?
- System Verilog RTL Source Code or Netlist format
- Testbenches
- Integration examples
- Software HAL & driver source code
- Software example
- Documentation
Specifications
Identity
Files
Note: some files may require an NDA depending on provider policy.
Provider

Learn more about Post Quantum IP core
Deploying StrongSwan on an Embedded FPGA Platform, IPsec/IKEv2 on Arty Z7 with PetaLinux and PQC
Mitigating Side-Channel Attacks In Post Quantum Cryptography (PQC) With Secure-IC Solutions
Nine Compelling Reasons Why Menta eFPGA Is Essential for Achieving True Crypto Agility in Your ASIC or SoC
Providing protection against EMFI attacks
A Comprehensive Post-Quantum Cryptography (PQC) Solution based on Physical Unclonable Function (PUF)
Frequently asked questions about Post-Quantum Cryptography IP cores
What is Post-Quantum Key Encapsulation IP Core?
Post-Quantum Key Encapsulation IP Core is a Post Quantum IP core from KiviCore listed on Semi IP Hub.
How should engineers evaluate this Post Quantum?
Engineers should review the overview, key features, supported foundries and nodes, maturity, deliverables, and provider information before shortlisting this Post Quantum IP.
Can this semiconductor IP be compared with similar products?
Yes. Buyers can compare this product with similar semiconductor IP cores or IP families based on category, provider, process options, and structured technical specifications.